SAP Security Notes March 2020: Two Critical Patches Released to Protect Solution Manager from Cyberattacks
Highlights of March SAP Security Notes analysis include:
- HotNews Note—Missing authentication in Solution Manager
- Onapsis Research Labs is Top Contributor—Detected and helped mitigate vulnerabilities rated with a CVSS 10 and 9.8
- Busy month for all SAP customers—4 HotNews Notes and 5 High Priority Notes released this month
It is the second Tuesday of the month, and that means it’s patch day for those of us that work in cybersecurity and are SAP customers. Today, you probably need to pay more attention, since SAP released several critical patches, including two critical patches for SAP Solution Manager (SolMan), both discovered and reported by the Onapsis Research Labs.
In both cases, a successful exploitation of these vulnerabilities could allow a remote unauthenticated attacker to execute highly privileged administrative tasks in the connected SAP SMD Agents, putting the confidentiality, integrity and availability of all systems at high risk. Also, the most critical vulnerability, with a CVSS of 10.0 (the highest possible value), may allow an attacker to also gain access to the full SAP landscape, by chaining this attack with other vulnerabilities. This is why this vulnerability has a CVSS of 10 compared to the 9.8 of the other critical vulnerability (scope is changed instead of unchanged in the CVSS vector).
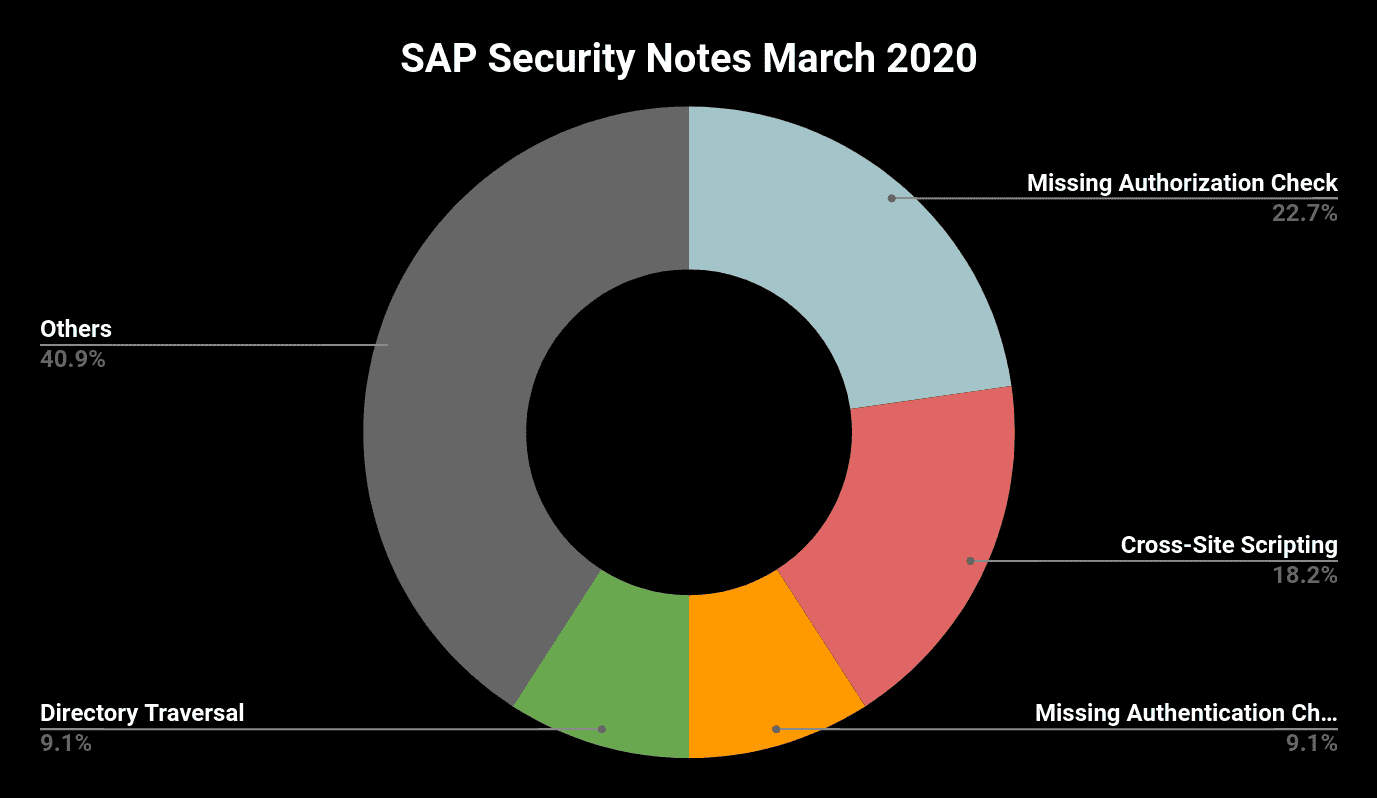
With another two critical releases, there is a total of four SAP Security Notes tagged as HotNews, all of them with a CVSS above 9.0, and also five High Priority Notes (CVSS above 7.0). That means that nine of the 22 notes released this month represent a significant risk if not applied. So, in summary, this month has:
- The most notes released this year (22),
- The most High Priority Notes (5) this year,
- The most HotNews (4) this year,
- Two critical vulnerabilities in Solution Manager that can be exploited by unauthenticated attackers, and
- The first SAP Security Note with CVSS 10.0 since SAP records the CVSS v3 score in the note.
With so many critical vulnerabilities, this month’s patching process should be treated with an increased priority to ensure SAP systems are protected. Let’s review some more details about the most critical vulnerabilities this month.
Missing Authentication in SAP Solution Manager Allows Potential Control Over Connected SAP Systems
Today, SAP patched one of the most critical vulnerabilities in recent history, and definitely the most critical one so far this year. SAP Security Note #2890213, titled “Missing Authentication Check in SAP SolMan (User-Experience Monitoring)” fixes a critical bug reported by Onapsis Researchers (Pablo Artuso and Yvan Genuer). This vulnerability has been scored with CVSS 10.0, the highest value for this standard, since its vector includes low attack complexity (AC), no privileges required (PR), changed scope (S) and high impact in Confidentiality (C), Integrity (I) and Availability (A), among others.
The purpose of SolMan is to centralize the management of all SAP and non-SAP systems that are within a landscape. As an administration solution, it performs actions such as implementation, support, monitoring and maintenance of the enterprise SAP solutions. All systems connected to SolMan are also known as satellite systems. If an SAP customer wants to fully utilize the capabilities of SolMan, they must install an application called Solution Manager Diagnostic Agent (SMDAgent) on each host where an SAP system is running. This agent manages communications, instance monitoring and diagnostic feedback to SolMan. The Onapsis Research team identified that in default configurations, an unauthenticated remote attacker could be able to execute operating system commands as the SMDAgent OS user on each satellite’s system and achieve full privileges on the associated SAP systems.
In order to patch this issue, customers should install the LM-SERVICE Software Component mentioned in the SAP Security Note. For companies whose patching process may take too long for a critical vulnerability, SAP offers a partial fix that can be implemented manually on the system. It is always recommended to deploy the complete fix through the component installation.
SAP Completes Patching for Critical Vulnerabilities in SMDAgent
SAP Security Note #2845377, titled “Missing Authentication Check in SAP Solution Manager (Diagnostics Agent)” is the latest patch of a series of related vulnerabilities reported by Onapsis researcher, Yvan Genuer, that SAP has started patching in July of 2019. This latest patch fixes the most critical vulnerability of the series. As it was explained before, with the vulnerabilities that were first fixed, a SolMan administrator could execute operating system commands and “obtain full control over an SAP system by compromising the SMDAgent user, allowing access to sensitive information (such as credentials and critical business information), changing application configurations or even stopping SAP services”. These vulnerabilities were fixed with SAP Security Notes #2808158 and #2823733.
By exploiting the vulnerability that was patched today, an attacker can bypass authentication. That means the attack can be executed by any person with access to the network, without need of a valid user in the SolMan system. Based on this, and the fact that SMDAgent is present in any SAP installation, the impact and criticality of this vulnerability is significantly higher, now with a CVSS of 9.8 since privileges required in CVSS vector is now “None”, versus “High” in the previous vulnerabilities.
SMDAgent is a technical component which does not directly handle sensitive data of the business. However, this vulnerability allows an attacker to perform sensitive actions, such as stopping the system (availability), changing the behaviors of the application (integrity) or accessing sensitive information. As with the other critical note explained above, an updated version of the LM-SERVICE Software Component should be installed for patching this one too. See the SAP Security Note for details.
Other Critical SAP Security Notes in March
In addition to the two SAP Security HotNews Notes discovered and mitigated thanks to the Onapsis Research Labs that were just explained, SAP has released two further HotNews Notes and five High Priority Notes:
HotNews Note #2806198, titled “Path Manipulation in SAP NetWeaver UDDI Server (Services Registry)” with a CVSS of 9.1, describes a serious Directory Traversal vulnerability in SAP NW UDDI Server. The vulnerability is caused by an incorrect validation of the path that is provided by a user when importing UDDI content via the Services Registry.
The periodically recurring HotNews Note #2622660 provides a new patch for SAP Business Client that includes the new Chromium version 80.0.3987.122. This version fixes 56 security issues, 10 of them rated as High. As discussed in the Onapsis February blog post, SAP Business Client now supports a Chromium version that has stricter Cookie Handling which might lead to the complete or partial outage of some SAP Web Applications.
The two High Priority Notes with the highest CVSS scores affect SAP Business Objects.
Note #2861301, with CVSS of 8.1, fixes a vulnerability that allows an attacker to execute code remotely on the SAP Business Object Server. Possible exploits range from unauthorized execution of arbitrary commands to completely crashing the application. Only the fact that the attacker needs to upload a malicious file to the platform before and that he or she must get another user to open the file prevents the issue from being rated with an even higher CVSS score.
SAP Security Note #2826782, rated with CVSS of 7.5, fixes a vulnerability in SAP Business Objects Mobile that was detected by the Onapsis Research Labs. A non-authenticated attacker could use a specially-crafted payload to send requests to some endpoints. These requests can cause a Denial-of-Service situation for the impacted components and thus prevent legitimate users from accessing the application.
There is another Security Note #2858044, titled “Missing Authorization check in SAP Disclosure Management” that is also rated with CVSS 7.5. This value is based on the high impact on confidentiality, integrity and availability. SAP rates the attack complexity here as High, thus preventing the vulnerability from becoming a HotNews Note.
The two remaining High Notes affect SAP Environment Health and Safety and SAP MaxDB/liveCache. While the first one, #1966029, fixes a Directory Traversal vulnerability that allows an attacker to read and/or overwrite arbitrary files on the remote server, the second one, #2660005, is a Note that was updated already at the end of February. This Note solves an SQL Injection vulnerability that is exposed to attackers with DBM operator privileges.
Summary & Conclusions
SAP has patched several critical vulnerabilities this Patch Tuesday, and customers have to act quickly to secure their business-critical applications. We at the Onapsis Research Labs are product to have helped SAP’s Product Security Response team proactively identify and mitigate these risks, in order to ensure all SAP customers can be better protected against insider and outsider threats..
As always, the Onapsis Research Labs is already updating the Onapsis Platform to incorporate the newly published vulnerabilities into the product so that our customers can protect their businesses.
For more information about the latest SAP security issues and our continuous efforts to share knowledge with the security community, subscribe to our monthly Defender’s Digest Onapsis Newsletter.
