Protecting Oracle E-Business Suite: Encrypt Web Interface (HTTPS)
After the release of our threat report about a critical vulnerability on “Unauthorized Business Data Exfiltration Vulnerability”, we are continuing our series of blogpost about Oracle E-Business Suite security. To keep our readers informed about security risks and mitigation techniques to Oracle’s biggest ERP, E-Business Suite (EBS), we will continue to publish blogs on a monthly basis. In our last publication we showed how to reduce the attack surface by whitelisting exposed JAVA files and today we are going to discuss configuring secure and encrypted web browsing through HTTPS protocol. Let’s first understand what it is and what is the difference with HTTP.
Hyper Text Transfer Protocol Secure (HTTPS) is the secure version of HTTP, the protocol over which data is sent between your browser and the EBS that you are connected to. The ‘S’ at the end of HTTPS stands for ‘Secure’. It means all communications between your browser and the website (EBS) are encrypted. HTTPS is often used to protect highly confidential online transactions like online banking and online shopping order forms. With simple configurations enabling this protocol, users can avoid attackers watching their traffic (such as a password in the login page).
Secure Sockets Layer (SSL) and its successor Transport Layer Security (TLS) are features that provide encryption of network traffic between the users browser and Oracle E-Business Suite web server. It is highly recommended to configure your Oracle E-Business Suite environment to use HTTPS (HTTP over TLS).
As of October 2014 (after the POODLE attack) all versions of SSL are considered by Oracle as insecure and should not be used. Oracle highly recommends that Oracle E-Business Suite customers migrate from SSL to TLS 1.2. Doing that, users will address a bunch of recent security vulnerabilities (such as POODLE, FREAK, LOGIAM, and RC4NOMORE, and others).
HTTPS 101: Terminology and Concepts
In order to move forward, make sure you fully understand the basic concepts and protocols related to HTTPS:
- Transport Layer Security (TLS): creates an encrypted connection between two machines allowing for private information to be transmitted without the problems of eavesdropping, data tampering, or message forgery
- Secure Sockets Layer (SSL): Defines the essential functions of mutual authentication, data encryption, and data integrity for secure transactions
- HTTP and HTTPS: HTTP is the primary communication protocol for the World Wide Web. HTTPS is a combination of HTTP and TLS.
- Certificate Authority (CA): is a trusted third party responsible for issuing, revoking, and renewing digital certificates
- Certificate Signing Request (CSR): Is a digital file which contains your public key and your name. You send the CSR to a Certifying Authority (CA) to be converted into a real certificate.
- Digital Certificate (Public Key): is a digital file that you generate as part of a key pair (private key and public key) and use to encrypt/decrypt messages.
- TLS Termination Point: A TLS termination point is the end-point server for the encrypted connection that has been initiated by a client (for example, a browser).
Types of Connections in EBS
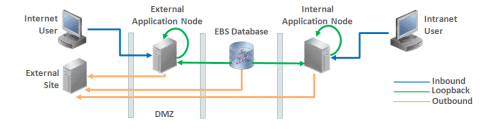
Oracle E-Business Suite connections fall into the following three categories: inbound, loopback and outbound connections; as it is shown in the following image.
- Inbound connections are from a client to the Oracle HTTP Server (OHS) delivered with the Oracle E-Business Suite applications technology stack. (Mobile, XML Gateway, accesses from browser and Forms Servlet mode.
- Loopback connections are from Oracle E-Business Suite back to the Oracle HTTP Server (OHS) delivered with the Oracle E-Business Suite applications technology stack (workflow, payments call back,opmn, OAM)
- Outbound connectionsare from Oracle E-Business Suite to external site(s). (iProcurement, isupply, payments credit card processing,etc.)
Of course all all types of connections can (and should be) secure, but the most important one is when there is an external site in a DMZ. In that scenario, a user will be connecting to the business-critical application through untrusted networks, which increase the need of properly protect data transfer.
If you expose any part of your Oracle E-Business Suite production system to the Internet, you can consult My Oracle Support Knowledge Document 1375670.1, which better describes the role of DMZs, external web tiers, external responsibilities, URL firewall, and reverse proxies in a secure external Oracle E-Business Suite deployment.
How to Check if HTTPS is Enabled in EBS
You can easily check if HTTPS is enabled on your environment by accessing E-Business Suite through a web browser. If it is, after trying to access the site through HTTP, you should be redirected to HTTPS or see a message like this one:
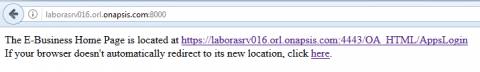
Also, the following query to the database can also confirm that HTTPS is properly enabled:
select decode(UPPER(SUBSTR(APPS.FND_WEB_CONFIG.PROTOCOL,1,5)), ‘HTTPS’,’HTTPS_ENABLED’, ‘HTTPS_DISABLED’) “SSL Mode” from dual;
Configure HTTPS in EBS
To be honest, to enable HTTPS in Oracle E-Business Suite is not an easy task, you will need to check all tiers in your system (client, database and Applications). Depending on the version, you will need to configure Weblogic (for 12.2.X) or apache (for 12.1.X), as well as necessary changes in many files in the environment, run autoconfig and restart services, among other things. But… it is very necessary and we highly recommend taking these steps for a secure configuration (if your use HTTP only, all your information transfer between the tier and clients would be without encryption and any attacker would be able to see that).
Here’s a list of some of the variables that is necessary to change in order to properly activate HTTPS and the value you should configure to make it works:
|
Variable |
Non-TLS Value |
TLS Value |
|
s_url_protocol |
http |
https |
|
s_local_url_protocol |
http |
https |
|
s_webentryurlprotocol |
http |
https |
|
s_active_webport |
same as s_webport |
same as s_webssl_port |
|
s_webssl_port |
not applicable |
default is 4443 |
|
s_https_listen_parameter |
not applicable |
same as s_webssl_port |
|
s_login_page |
url constructed with http protocol and s_webport |
url constructed with https protocol and s_webssl_port |
|
s_external_url |
url constructed with http protocol and s_webport |
url constructed with https protocol and s_webssl_port |
Finally, the value of s_webport is already configured before activation so it could remain in the same state unless you would like to configure a non-default port. If not, there is no need to configure this value.
Conclusion
In previous post we reviewed the importance of the password policy and now we see another important and basic fixture about security. The Https is the future of web applications security, as it is no longer secure without “s” (https).
If you are moving forward (and we expect you will), you should read the full procedure in the following documents (based on your version):
- 376700.1, Enabling TLS in Oracle E-Business Suite Release 12.1.
- 1367293.1, Enabling TLS in Oracle E-Business Suite Release 12.2.
The Onapsis Platform for Oracle EBS provides an effective and efficient solution to align IT, security and compliance teams by automating manual tasks and streamlining processes required to maximize availability and keep you protected and compliant. Learn more or request a demo.
