Defending the SAP Supply Chain: 7 Security Best Practices for Transport Management
What is SAP Transport Management?
SAP Transport Management (SAP TMS) orchestrates the movement of objects and software changes across SAP systems, ensuring enterprise consistency while presenting unique cybersecurity challenges.
SAP Transport Management functions as the primary vehicle for organizations to effectively manage changes to SAP landscapes. This critical function allows administrators to implement updates smoothly, minimizing disruptions to core business processes. The deployment process begins in the development system, where developers first introduce custom code and configuration changes. From there, SAP TMS facilitates the organized migration of these changes through testing environments and ultimately into production systems.
This structured approach acts as a safeguard against structural errors and data inconsistencies that plague systems updated in a haphazard manner. Furthermore, SAP TMS increases operational cybersecurity when configured correctly alongside dedicated SAP DevSecOps practices. With robust measures to protect against unauthorized access and potential data breaches, it serves as an integral component of an enterprise cybersecurity strategy. SAP Transport Management ensures the integrity, security, and continuous improvement of critical business operations. As enterprises increasingly rely on SAP systems, the role of SAP TMS in maintaining a stable and secure environment remains paramount.
How does SAP Transport Management Work?
SAP Transport Management governs the movement of software and configuration changes cascading across development, testing, and production environments.
A transport request packages the changes made in a development system. This request includes all required details, such as the altered objects, the SAP version, and the specific target system receiving the application updates.
Relevant stakeholders, such as developers, quality assurance personnel, and project managers, review and approve the transport request. Once approved, the request is released for migration to the target system.
The transport request migrates to the target system, where the application changes execute. The target system typically functions as a dedicated testing or production environment.
After the changes deploy, security and development teams test the configurations to ensure they function as intended and do not negatively impact other areas of the SAP ecosystem.
Once the changes achieve successful verification, administrators close the transport request to finalize the deployment cycle.
Why Should Organizations Use SAP Transports?
Integrating transports into the software development lifecycle standardizes application deployments but creates overlooked vulnerabilities requiring specialized security oversight.
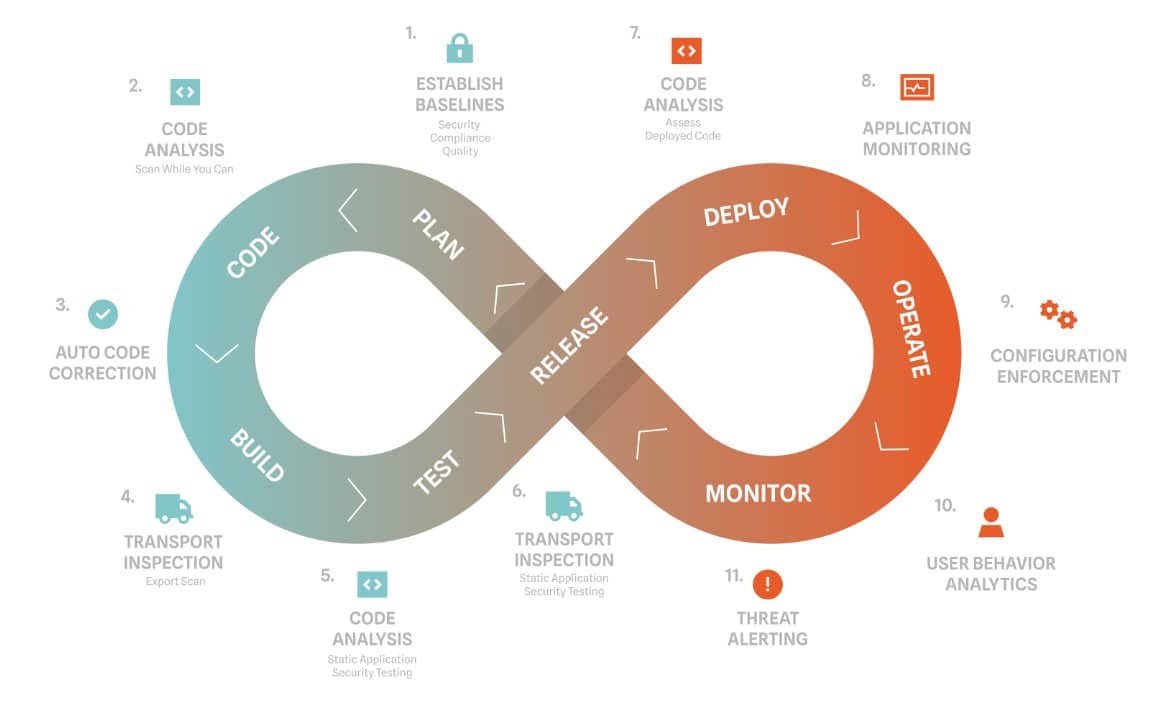
Integrating security into each step of the development lifecycle requires organizations to adopt tools like SAP Transport Management. Transports deploy at multiple points in the development cycle, as shown in the DevSecOps diagram below. Because transports execute continuously throughout the development pipeline, they frequently represent an overlooked aspect of SAP security, creating distinct opportunities for exploitation across critical SAP applications. Even with appropriate access management established, an attacker can leverage numerous techniques to compromise production systems through malicious transports. This exploitation directly results in the catastrophic loss of data confidentiality, system integrity, and operational availability.
What Security Teams Should Know about SAP Transport Management
Managing enterprise systems requires balancing operational automation with rigorous risk management to mitigate specific transport vulnerabilities.
To mitigate these risks, it’s important to implement proper access controls, use secure transport protocols, monitor and audit transport activities, and ensure proper segregation of duties. Additionally, implementing encryption and digital signatures can help ensure the integrity and confidentiality of transport requests.
Onapsis for SAP Transport Management
Securing the SAP backend development system holistically requires automated application security testing to inspect transports prior to production deployment.
Onapsis Control automates the monitoring of changes that are leaving the development system and provides additional approval workflows for critical situations. Control is ideal for enterprises who want to:

Ready to eliminate your SAP cyber security blindspot?
Let us show you how simple it can be to protect your business applications.
Frequently Asked Questions
What is the primary function of SAP Transport Management?
SAP Transport Management orchestrates the continuous movement of software and configuration changes across development, testing, and production environments. This structured deployment function ensures system consistency, prevents application conflicts, and minimizes disruptions to core business processes during updates.
What are the main security risks associated with SAP transports?
Key security risks include unauthorized user access, insecure transport protocols, and the potential exposure of sensitive data packaged within transport requests. Additional vulnerabilities stem from a lack of continuous monitoring, auditing blind spots, and failing to enforce strict segregation of duties across the software development lifecycle.
How do organizations secure SAP transport routes?
Organizations secure transport routes by deploying advanced firewalls, virtual private networks, and secure file transfer protocols such as SFTP and HTTPS. Utilizing robust encryption and digital signatures further guarantees the integrity and confidentiality of transport requests while in transit between environments.
Why is automated monitoring necessary for SAP Transport Management?
Automated monitoring detects unauthorized access and malicious modifications to transport requests that manual auditing processes consistently miss. Integrating continuous application-layer monitoring ensures security teams can instantly identify anomalies, review audit logs, and maintain strict compliance with corporate security policies prior to production releases.
How does Onapsis monitor changes within SAP systems?
Onapsis monitors SAP system changes through continuous automated application security testing and real-time threat detection across the entire development lifecycle. The platform inspects custom code and transport requests prior to production release using the Onapsis Control module, identifying structural errors and security vulnerabilities. Once deployed, the system continuously monitors the application layer, feeding SAP-specific telemetry directly into corporate SIEM platforms to detect unauthorized changes and active exploitation attempts instantly.
Are there cybersecurity solutions that provide monitoring for changes in SAP applications?
Yes, specialized cybersecurity solutions exist to natively monitor the proprietary SAP application layer for unauthorized changes and malicious activity. General-purpose network scanners and security tools lack the capability to interpret proprietary SAP protocols and ABAP programming logic. Organizations must deploy purpose-built SAP security platforms to achieve continuous visibility into the application layer. These specialized solutions automate vulnerability management, scan transport requests, and orchestrate real-time incident response to protect critical enterprise data.
