TMSADM User with Default Password: Another Risk in Your SAP System

As our readers know, we continuously share details to raise awareness and enable organizations to further secure their SAP cybersecurity infrastructure. In this specific blog, we will focus on one of the well-known SAP default users: TMSADM. What the security implications are of having it enabled with default passwords, and how to properly protect it? As you can imagine, it is not as simple as it sounds, so that’s why we created this blogpost for you.
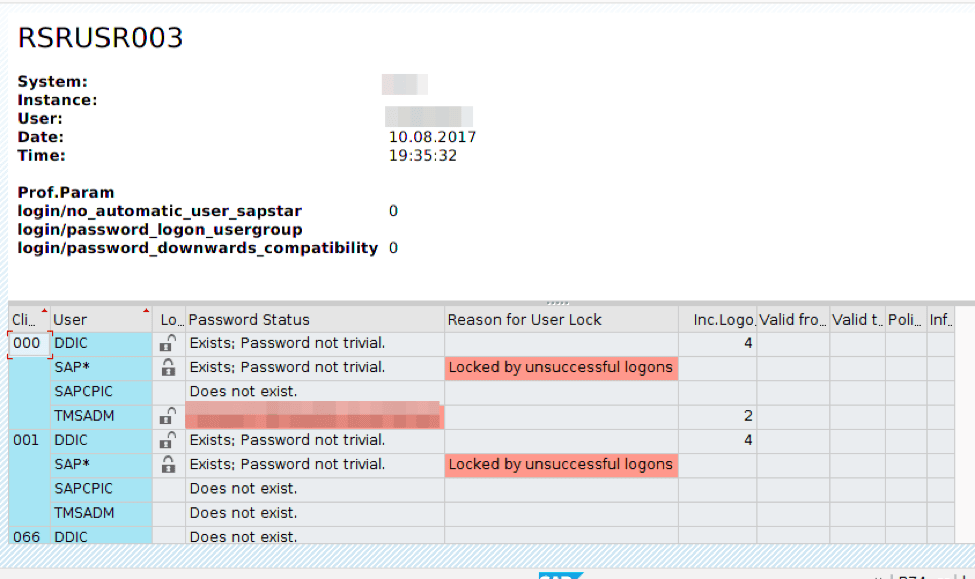
Whenever a new SAP system is built, upgraded, copied or restored from backup, one of the very first tasks a SAP security administrator should do is to check whether this default user, provided by SAP, has had its default password changed, locked or (in some cases), removed. In short, TMSADM is a system user created on all ABAP systems in client 000 when Transport Management System (TMS) is configured, as shown in the following table:
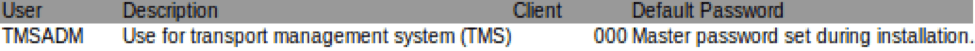
Whenever TMS is configured, the user TMSADM is created. While we will not fully explain the functionality of TMS we do think it is important at least to mention how this user is created by default. SAP normally follows a system landscape with a 3-tier architecture such as DEV (development), QAS (quality), PRD (production). One of the systems has to be configured as a transport domain controller and this configuration has to be done as a part of implementation. The transaction to configure transport management is STMS:
The TMS automatically generates RFC connections between the systems in a domain so that they can communicate. Within a transport domain, all the SAP systems can communicate with each other using RFC. Data is exchanged between the systems using the RFC connections of the TMS.
About the TMSADM user
The TMSADM user is used for transfers through the transport system. It is created automatically upon configuration of Transport Management System (TMS) via the 000 client. TMSADM is a system user with authorizations limited to a certain display and TMS configuration activities. TMSADM has display authorizations for the following:
- system properties
- transport configuration
- transport logs and data files (content of transport requests)
- import queues
TMSADM is a communication user because it is used for the distribution of transport configuration changes to systems of the current transport domain. In other words, user TMSADM enables you to distribute the basic configuration to all SAP systems in the domain on the domain controller and to display the import queue. The default profile for the user is S.A_TMSADM which enables to utilize RFC-functions within the GUI and to write to a file system. You must never extend this profile or add a profile or role of your own to the user.
As other default users, TMSADM has a default password.
Understanding the risk of TMSADM Default Password
As noted in the previous paragraph, the default password of the TMSADM user is well known and can thus easily be guessed. After correctly guessing the password, an adversary may remotely start RFC requests to perform critical actions such as deleting and reading files (EPS_DELETE_FILE, EPS_OPEN_FILE2) or may execute arbitrary ABAP code through the RFC_ABAP_INSTALL_AND_RUN or TTMS_CI_START_SERVICE function vulnerabilities. Furthermore, using BAPI_USER_CREATE1 and SUSR_RFC_USER_INTERFACE requests an adversary may create a dialog user and consequently enter the system with unlimited access to business data.
To properly check the password of TMSADM through SAP GUI, you can use report RSUSR003. It is used to make sure that the TMSADM user has been created and that the default password has been changed for this user. Follow these steps to run this RSUSR003 report:
1. Go to transaction SE38. This results in the following screen being shown:
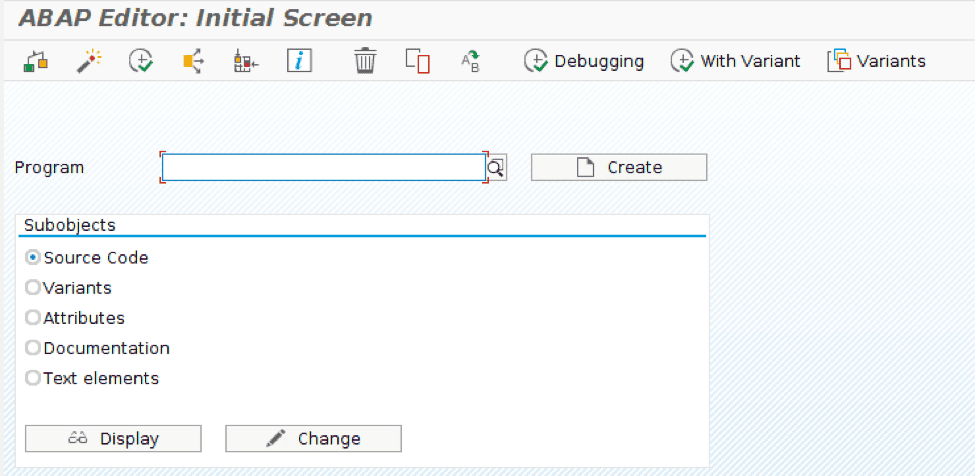
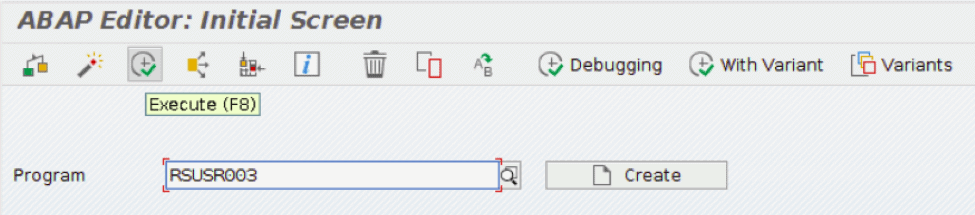
2. Enter RSRUSR003 in the program field and click the Execute button or press F8.
OPTIONAL: If necessary, uncheck Display Profile parameters and execute F8.
3. You will see the list of default SAP users indicating whether the user is locked and if the password has been changed from its default value.
How to protect TMSADM?
During the past few years, SAP has published different notes explaining ways to change the TMSADM user password. One of the most interesting is 1414256 – Changing TMSADM password is too complex. Time has passed however, and the solution has changed. The correct solution can be found below. In order to change the TMSADM user password, you must follow these steps:
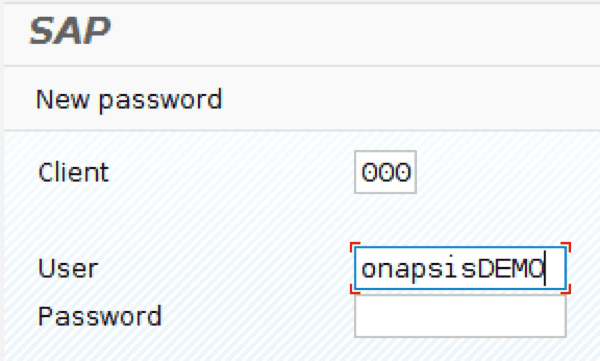
1. Enter the 000 client, while being logged in as an administrator.
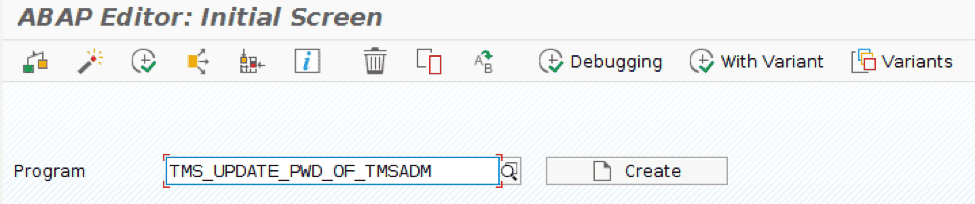
2. Run transaction SE38 and start the TMS_UPDATE_PWD_OF_TMSADM program.
3. Insert a password in the fields as shown below:
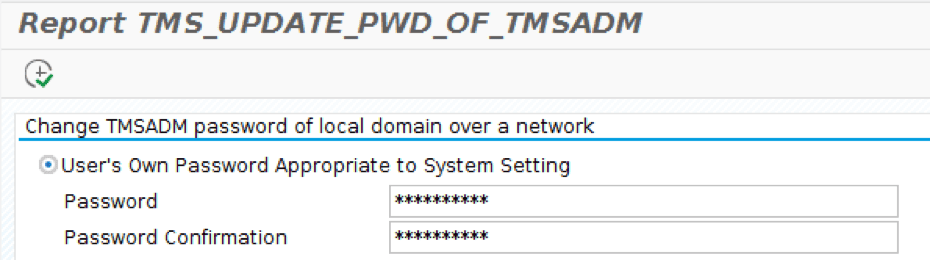
Make sure that this user belongs to the SUPER group in all clients. This way you will be certain that only authorized administrators have the right to change this user’s account.
Conclusions
It’s important to understand the risks of not changing the TMSADM default password. It’s known that security researchers have been able to access default SAP accounts on enterprise systems worldwide by using default passwords. In fact, one of the first “doors” that an unauthorized user will try to open is the well-documented and published default passwords of the standard database.
Perform regular checks for your clients to eliminate the risk of illicit access. Onapsis Security Platform (OSP) can help you to be protected against this and others attacks. Our tool is able to detect not only vulnerable default users, such as TMSADM, but a big variety of different vulnerabilities also associated with default users. As well as with TMSADM, there are other users that are configured with default password. And, as we have shown before, an unauthorized user could login using these accounts and have access to the system.
