SAP Security Notes: May 2026 Patch Day
HotNews SAP Security Notes released for SAP Commerce Cloud and SAP S/4HANA
Highlights of May SAP Security Notes analysis include:
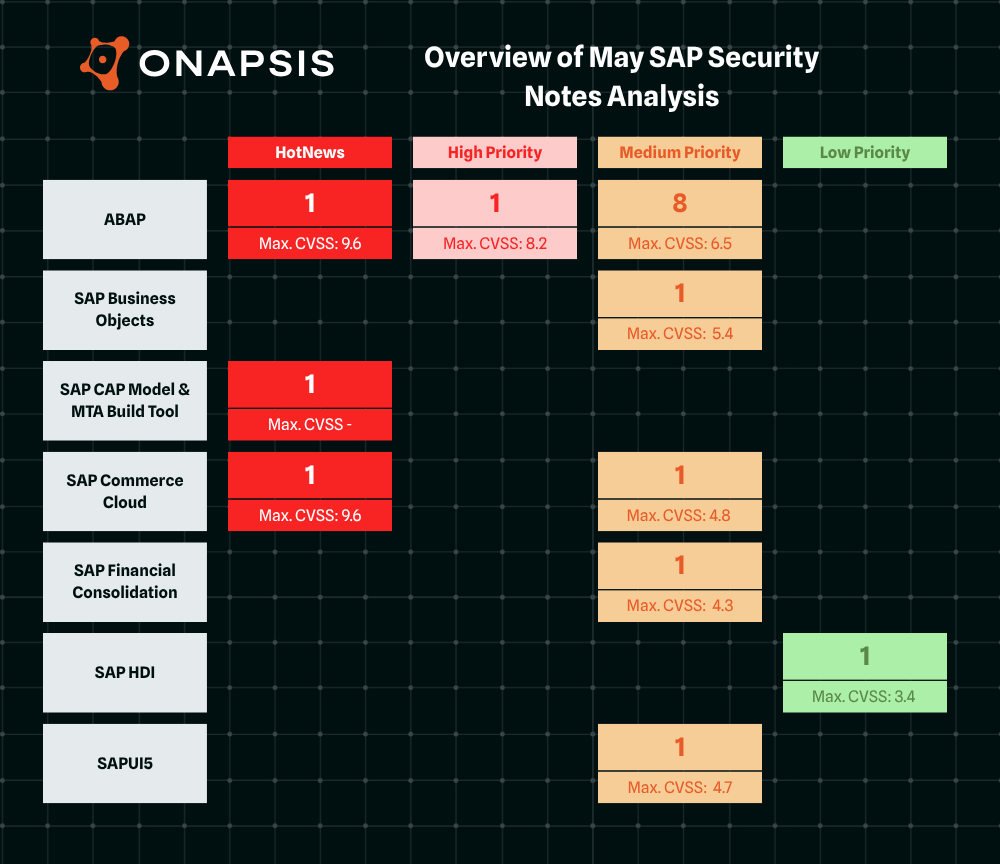
- May Summary – Seventeen new and updated SAP security patches released, including three HotNews Notes and one High Priority Note
- Supply Chain Attack – Attackers use manipulated npm packages to steal sensitive data
- Onapsis Research Labs Contribution – Our team supported SAP in patching seven vulnerabilities, covered by three SAP Security Notes
SAP has published seventeen new and updated SAP Security Notes in its May Patch Day, including three HotNews Notes and one High Priority Note. Three SAP Security Notes were published in contribution with the Onapsis Research Labs.
The HotNews Notes in Detail
On April 30, 2026, SAP released HotNews Note #3747787 addressing a supply chain attack targeting SAP developers and organizations using the SAP Cloud Application Programming (CAP) model. Identified as a variant of the “Shai-Hulud” worm, this attack involves the injection of malicious code into widely used SAP npm packages. The primary goal of this malware is the automated theft of cloud credentials, service tokens, and private keys. The malicious packages were available for a two to four hour window on April 29, 2026. If one of your developers downloaded the specific package(s) during the time window in which the malicious versions were available, then you may be affected. Clean versions of the packages were released to supersede the infected versions. More details about the attack can be found here.
SAP Security Note #3733064, tagged with a CVSS score of 9.6, patches a Missing Authentication Check vulnerability in SAP Commerce Cloud configuration. The vulnerability is caused by an overly permissive security configuration with improper rule ordering, allowing an unauthenticated user to perform malicious configuration upload and code injection, resulting in arbitrary server-side code execution.
SAP Security Note #3724838, tagged with a CVSS score of 9.6, provides a patch for an SQL injection vulnerability in SAP S/4HANA (SAP Enterprise Search for ABAP). Due to improper or missing input validation and sanitization, an authenticated attacker is able to inject malicious SQL statements through user-controlled input with high impact on the confidentiality and availability of the application. Fortunately, the affected source code only allows read access to data so that integrity is not impacted.
The High Priority Notes in Detail
The only High Priority Note of SAP’s May Patch Day has been released by SAP in collaboration with the Onapsis Research Labs(ORL). The note patches five function modules in SAP Forecasting & Replenishment that allows an authenticated attacker with administrative authorizations to execute arbitrary operating system commands. The function modules are not remote-enabled but they accept user input from upstream components. SAP Security Note #3732471, tagged with a CVSS score of 8.2, patches the vulnerabilities by adding proper authorization checks and input validation.
Onapsis Contribution
In addition to High Priority Note #3732471, the ORL team supported SAP in fixing another two Medium Priority vulnerabilities.
SAP Security Note #3721959, tagged with a CVSS score of 5.4, patches a Missing Authorization Check vulnerability in SAP Strategic Enterprise Management (BSP application Balanced Scorecard Wizard). Due to a missing authorization check, an authenticated attacker could access information that they are otherwise unauthorized to view. The vulnerability also allows the attacker to change the default settings and modify value fields, which will mislead risk evaluations and falsely lower assessed risk levels.
SAP Security Note #3728690, tagged with a CVSS score of 4.7, addresses a Reflected Cross-Site Scripting (XSS) vulnerability in SAP NetWeaver Application Server ABAP (Applications based on Business Server Pages). Our team detected that a specific URL parameter was not properly encoded, enabling an unauthenticated attacker to embed a malicious script into the affected URL. If a victim clicks the manipulated link, the injected input is processed during web page generation, resulting in the execution of malicious content in the victim’s browser context. A successful exploit allows the attacker to read and/or modify information, impacting the confidentiality and integrity of the application.
Summary & Conclusions
With seventeen SAP Security Notes, including three HotNews Notes and one High Priority Note, SAP’s May Patch Day is an average one.The supply chain attack at the end of April caused considerable turbulence, and it remains to be seen whether such attacks will recur in the future. It is therefore all the more important to always apply critical patches promptly.
| SAP Note | Type | Description | Priority | CVSS |
| 3747787 | New | Malicious open-source packages in SAP Cloud Application Programming Model & MTA Build Tool BC-XS-CDX-NJS | HotNews | – |
| 3733064 | New | [CVE-2026-34263] Missing authentication check in SAP Commerce Cloud configuration CEC-SCC-CDM-BO-APP | HotNews | 9.6 |
| 3724838 | New | [CVE-2026-34260] SQL injection vulnerability in SAP S/4HANA (SAP Enterprise Search for ABAP) BC-EIM-ESH | HotNews | 9.6 |
| 3732471 | New | [CVE-2026-34259] OS Command Injection Vulnerability in SAP Forecasting & Replenishment SCM-FRE-FRP | High | 8.2 |
| 3730019 | New | [CVE-2026-40135] OS Command Injection vulnerability in SAP NetWeaver Application Server for ABAP and ABAP Platform BC-ABA-SC | Medium | 6.5 |
| 3680767 | New | [CVE-2026-34264] Information Disclosure vulnerability in SAP Human Capital Management for SAP S/4HANA PA-PA-XX | Medium | 6.5 |
| 3718083 | New | [CVE-2026-40133] Missing Authorization check in SAP S/4HANA Condition Maintenance SD-MD-CM | Medium | 6.3 |
| 3727717 | New | [CVE-2026-40137] Cross-Site Scripting (XSS) vulnerability in Business Server Pages Application (TAF_APPLAUNCHER) SV-SMG-TWB-CBT | Medium | 6.1 |
| 3721959 | New | [CVE-2026-40132] Missing Authorization Check in SAP Strategic Enterprise Management (BSP application Balanced Scorecard Wizard) FIN-SEM-CPM-BSC | Medium | 5.4 |
| 3667593 | New | [CVE-2026-0502] Cross Site Request Forgery (CSRF) in SAP BusinessObjects Business Intelligence Platform BI-BIP-INV | Medium | 5.4 |
| 3716450 | New | [CVE-2025-68161] Potential Improper Certificate Validation in SAP Commerce Cloud (Apache Log4j) CEC-SCC-PLA-PL | Medium | 4.8 |
| 3728690 | New | [CVE-2026-27682] Reflected Cross-Site Scripting (XSS) vulnerability in SAP NetWeaver Application Server ABAP (Applications based on Business Server Pages) BC-BSP | Medium | 4.7 |
| 3726583 | New | [CVE-2026-34258] Content Spoofing vulnerability in SAPUI5 (Search UI) HAN-AS-INA-UI | Medium | 4.7 |
| 3735359 | New | [CVE-2026-40129] Code Injection vulnerability in SAP Application Server ABAP for SAP NetWeaver and ABAP Platform BC-MID-ICF | Medium | 4.3 |
| 3713521 | New | [CVE-2026-40136] Denial of service (DoS) in SAP Financial Consolidation EPM-BFC-PSI | Medium | 4.3 |
| 3718508 | New | [CVE-2026-40134] Missing Authorization Check in SAP Incentive and Commission Management ICM | Medium | 4.3 |
| 3726962 | New | [CVE-2026-40131] SQL Injection vulnerability in SAP HANA Deployment Infrastructure (HDI) deploy library HAN-DB-DI | Low | 3.4 |
As always, the Onapsis Research Labs is already updating The Onapsis Platform to incorporate the newly published vulnerabilities into the product so that our customers can protect their businesses.
For more information about the latest SAP security issues and our continuous efforts to share knowledge with the security community, subscribe to our monthly Defender’s Digest Onapsis Newsletter.
