Operationalizing DORA Compliance: Securing SAP Against the 5 Core Pillars

With the Digital Operational Resilience Act (DORA) in active enforcement, financial entities must transition from theoretical governance to technical execution. Integrating these stringent mandates into a comprehensive SAP GRC strategy is essential. Regulators require definitive proof that critical infrastructure, including enterprise SAP environments, can withstand and recover from severe cyber incidents.
This technical guide dissects the operational obligations of DORA and maps them directly to the automated SAP security capabilities required to achieve and maintain compliance.
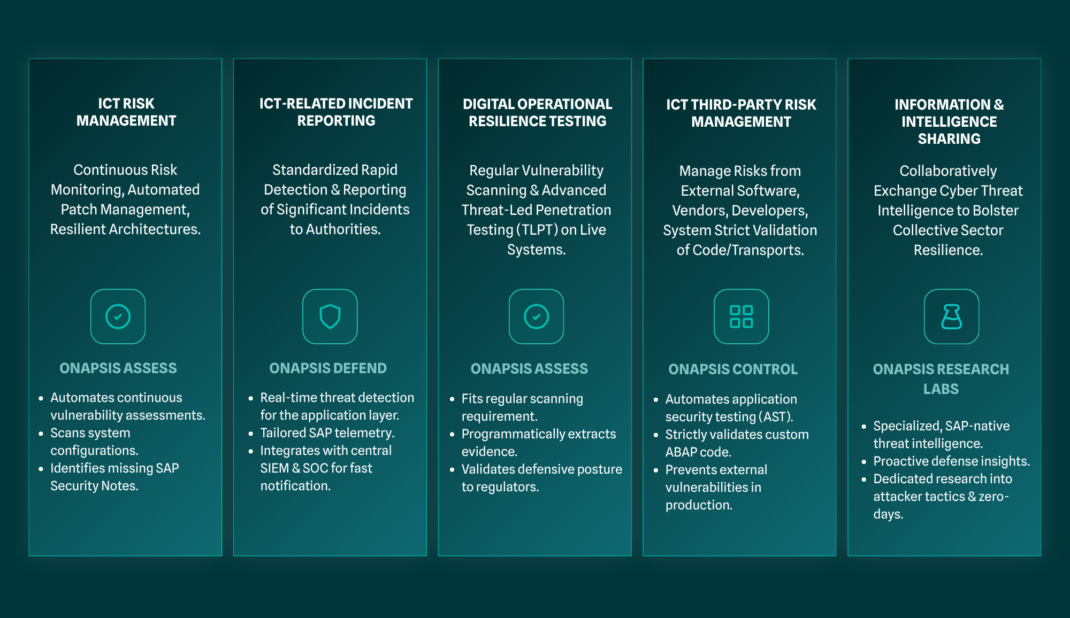
Aligning SAP Security with the 5 Pillars of DORA
The Digital Operational Resilience Act is built upon five foundational pillars requiring financial entities to implement continuous risk management, rapid incident reporting, and advanced resilience testing across all critical ICT systems.
Securing SAP environments under DORA requires organizations to map their technical security controls directly to the regulatory framework.
Pillar 1: ICT Risk Management
DORA mandates the continuous monitoring of Information and Communication Technology (ICT) risks, requiring organizations to maintain resilient architectures and automated patch management protocols. For SAP environments, this necessitates continuous vulnerability assessments and strict configuration monitoring. Security teams must systematically identify missing SAP Security Notes, insecure system configurations, and authorization flaws to harden the application layer against exploitation. Leveraging solutions like Onapsis Assess provides “automated visibility” to enforce secure baselines. It handles the continuous identification of missing SAP Security Notes, misconfigurations, and authorization flaws to meet the mandate for resilient architecture.
Pillar 2: ICT-Related Incident Reporting
Financial entities must detect and report significant ICT-related incidents to regulatory authorities within strict timeframes. Achieving these notification thresholds requires real-time threat detection capabilities specifically tailored for the SAP application layer. Organizations must integrate SAP telemetry directly into corporate Security Information and Event Management (SIEM) solutions. Utilizing Onapsis Defend acts as the bridge between SAP and the SIEM. It captures raw event details (telemetry) from the SAP application layer so the SOC can detect threats in real-time and meet DORA’s strict reporting deadlines.
Pillar 3: Digital Operational Resilience Testing
The regulation requires regular vulnerability scanning and, for significant entities, advanced Threat-Led Penetration Testing (TLPT) on live production systems. Integrating automated vulnerability management provides continuous proof of resilience. Security teams utilizing Onapsis Assess can execute continuous scans across the SAP architecture to validate defensive postures and ensure vulnerabilities are remediated before threat actors can exploit them.
Pillar 4: ICT Third-Party Risk Management
Organizations must rigorously manage the risks introduced by external software providers, system integrators, and third-party developers. Because SAP environments rely heavily on custom ABAP code and external application integrations, organizations must deploy automated application security testing (AST). Validating custom code and third-party “transports” (software updates/changes) with Onapsis Control before deployment into production environments prevents external vulnerabilities from compromising the core ERP system.
Pillar 5: Information and Intelligence Sharing
DORA encourages financial entities to securely exchange cyber threat intelligence to bolster the collective resilience of the European financial sector. Leveraging specialized, SAP-native threat intelligence empowers organizations to actively participate in these sharing arrangements. Accessing dedicated research from the Onapsis Research Labs regarding zero-day exploits and attacker tactics allows financial institutions to anticipate threats and apply proactive defensive controls. It allows firms to see zero-day exploits and attacker tactics early, meeting the DORA goal of proactive intelligence sharing.
Automating the Technical Validation of DORA Compliance
Automating security operations allows financial entities to continuously validate their defensive posture, providing the technical proof of resilience demanded by regulatory authorities.
Manual compliance audits fail to provide the real-time visibility required by DORA. Regulators expect organizations to demonstrate continuous control over their critical ICT environments. The Onapsis Platform operationalizes this requirement by continuously assessing the SAP landscape against the latest threat intelligence.
While financial entities adapt to specific DORA mandates, organizations can leverage existing out-of-the-box compliance checks for rigorous parallel standards like NIS2 and NIST. This establishes the foundational vulnerability management and configuration governance required to prove operational resilience to internal and external auditors. The Onapsis Platform acts as the centerpiece of automating the 5 Pillars of Dora.
Frequently Asked Questions
How does DORA Pillar 1 apply to SAP systems?
Pillar 1 requires organizations to establish robust ICT risk management frameworks, which translates directly to continuous vulnerability management and patch application within the SAP landscape. Security teams must automate the identification and remediation of misconfigurations and missing SAP Security Notes to maintain a resilient architecture.
Why is SIEM integration necessary for DORA Pillar 2?
DORA Pillar 2 mandates rapid incident reporting, making it mandatory for organizations to feed SAP threat telemetry directly into their central SIEM platforms. This integration allows SOC teams to detect application-layer attacks in real time and meet strict regulatory notification deadlines.
What is Threat-Led Penetration Testing (TLPT) under DORA?
Threat-Led Penetration Testing is an advanced resilience testing requirement under Pillar 3 where organizations simulate sophisticated cyberattacks on live production systems. For SAP environments, this requires identifying existing vulnerabilities and demonstrating the capability to detect and respond to active exploitation attempts.
How do organizations manage third-party risk in SAP?
Managing third-party risk under DORA Pillar 4 requires financial entities to rigorously scan custom ABAP code and transports provided by external developers. Automated application security testing prevents system integrators from inadvertently introducing critical vulnerabilities into the core ERP environment.
