SAP Security Notes November 2016 – The Return of OS Command Injection
Today SAP published 13 Security Notes, two of which were tagged as ‘Hot News’ items. These two bugs were discovered a few months ago by the Onapsis Research Labs and represents the most critical updates to patch in order to properly protect your SAP Systems. Both notes are related to code injection attacks, which we’ve recently published advisories for, and have discussed in detail here.
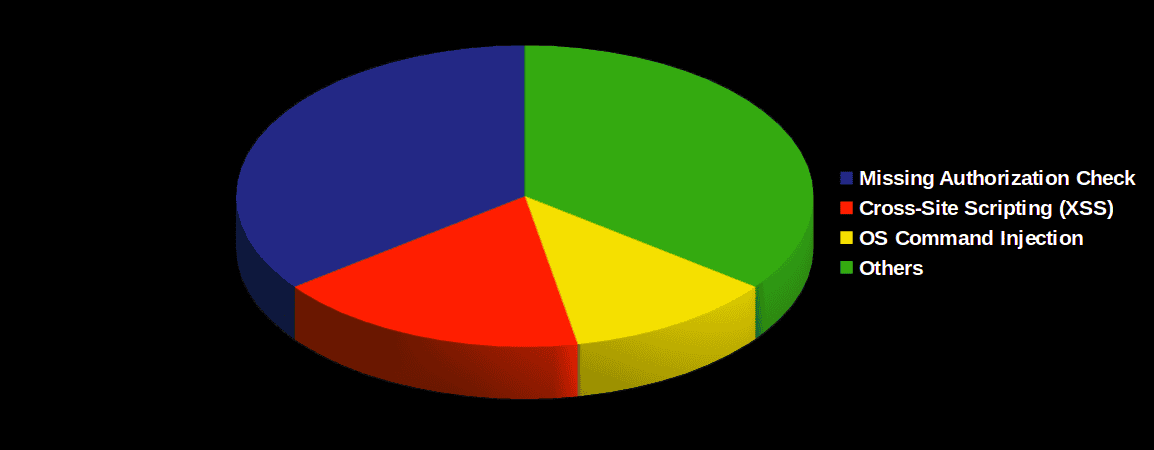
As with every second Tuesday of each month, SAP publishes new SAP Security Notes to keep systems updated with code improvements that solve different types of vulnerabilities. Since the last patch Tuesday and today, SAP has published 17 new Security Notes including several different types of vulnerabilities that were fixed: Code Injection, Denial Of Server, Missing Authority Check and Cross-Site-Scripting (XSS), among others:
Although there were not a lot of vulnerabilities solved this month, (it is the first month with less than 20 notes since May), that doesn’t mean that this is a reason to relax. Below, you can see the priority and severity for this month’s patched SAP security notes:
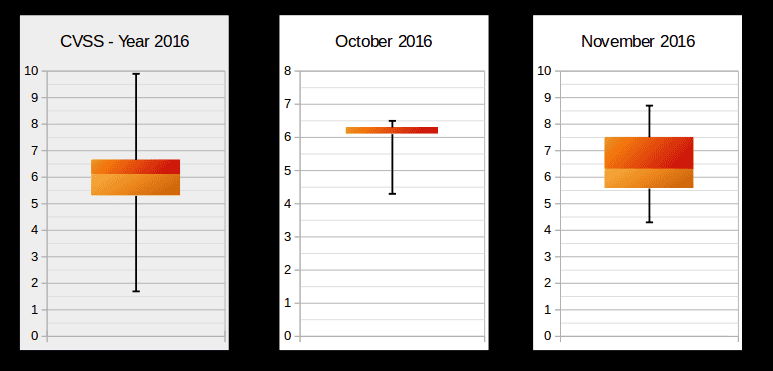
As shown, the severity of this month’s SAP security notes is high enough to prioritize the implementation of patches as soon as possible. It’s significant that two of the vulnerabilities for this month are marked as ‘hot news’ items, as SAP has not released any hot news items since July 2016, and are the 2 of nine total hot news items published in 2016 (four of them reported by Onapsis).
Hot news: Code & OS Command Injection
As been mentioned, this month has two hot news notes are the result of Onapsis Research Labs discoveries. Both relate to code injection attacks and are tagged with high risk CVSS v3 Scores of 9.1 points. This is because both vulnerabilities could compromise all confidentiality, availability and integrity on vulnerable systems. As shown in a previous blogpost on OS Command Injection, both notes correct improper sanitization on parameters for OS commands. If not corrected, an attacker would be able to include new commands adding special characters, as shown in the example below: (custom function created for awareness purpose)
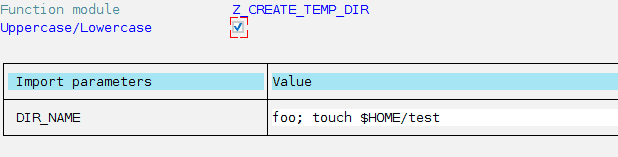
In the previous image, the function is waiting for a value to access a directory, but only by adding a symbol “;”,an attacker can add a new command to be executed in the remote system.
The first vulnerability fixed this month, Code Injection vulnerability in Text Conversion (2371726), was fixed by only allowing valid specific characters as parameter, eliminating the chance to include additional commands to execute. In the second vulnerability, OS Command Injection vulnerability in Report for Terminology Export (2357141), affected code lines were directly deleted since they are obsolete and there is no need to keep them.
In both cases, there aren’t any additional steps required for the note to take effect, so its implementation only needs to include installation of the SAP Security Notes. It is important to mention that both notes required specific privileges and cannot be exploited by any users or even anonymous attackers. Despite this fact, inside attackers should still be considered in any threat model or protection schema.
High Priority SAP Notes
In addition to the two hot news items mentioned above, there are also two SAP Security Notes categorized as high priority:
- Information Disclosure in SAP Software Update Manager (2366512): This note corrects the appearance of plain text passwords in certain log files. Despite defined CVSS risk being based on high confidentiality compromise, this type of vulnerability could lead not only to information disclosure, but could also lead to identity theft, bigger frauds and other integrity risks, depending on the user that has access to this information and the privileges of the disclosed passwords. CVSS v3 Base Score: 7.5 / 10
- Denial of service (DOS) in Message Server (2358972): For this type of vulnerability, risk is based on the availability issues. In this particular case, and depending on your SAP configuration, an availability problem on Message Server could lead to a user not being able to login on the system. CVSS v3 Base Score: 7.5 / 10
The Onapsis Research Labs are currently in the process of updating the Onapsis Security Platform to incorporate these newly published vulnerabilities. This will allow you to check whether your systems are up to date with these latest SAP Security Notes, and ensures that those systems are configured with the appropriate level of security to meet your audit and compliance requirements. Stay tuned for next month’s SAP Security Notes analysis.
Pablo Artuso, our young researcher, was recognized in this month’s SAP Acknowledgments page for his discovery of the two ‘hot news’ vulnerabilities. Congrats Pablo! Stay tuned for next month’s SAP security notes analysis.
