Oracle fixes 136 Software Vulnerabilities in April 2016
As a company, Onapsis is focused on securing business-critical applications such as SAP and Oracle. An important part of our research relies on identifying, and reporting on critical vulnerabilities in Oracle business applications in order to help Oracle customers reduce the risk to their organization.
This post analyzes the April 2016 Oracle Critical Patch Update (CPU) in order to provide Oracle customers with detailed information about the latest vulnerabilities affecting Oracle business critical applications. In addition, this post will help customers to better understand and prioritize the implementation and testing of vulnerabilities on these systems within their organization.
In April 2016, Oracle published 136 fixes which affect 49 different Oracle products. New to this month, Oracle used the Common Vulnerability Scoring System V2 (CVSS) and Common Vulnerability Scoring System V3 (CVSS) to measure the risk implied by the vulnerability such as exploitability, complexity and different aspects of impact. An important remark on this topic is that Oracle claimed this will be the only Oracle Critical Patch Update that will include both CVSS V2 and CVSS V3. Future CPUs will only include CVSS V3.
 In this month’s CPU, there are two important facts to highlight:
In this month’s CPU, there are two important facts to highlight:
1. More than 45% of the fixed vulnerabilities directly affect Oracle Business-Critical Applications.
2. More than half of the reported vulnerabilities (52.94%) can be exploited remotely without authentication (no username or password are required).
Because of this, the information and processes that are managed by Oracle applications could be at risk of exposure if the patching procedure is not followed, and Oracle applications are not updated. Companies running Oracle software and Oracle customers should take immediate actions to mitigate these risks.
The Onapsis Research Labs discovered and reported several of these vulnerabilities to Oracle. In the current CPU, Oracle fixed four vulnerabilities affecting Oracle E-Business Suite that were reported by Onapsis. These vulnerabilities are CVE-2016-3437, CVE-2016-3436, CVE-2016-3438 and CVE-2016-3439.
The business critical applications affected by the vulnerabilities fixed in the current CPU are: Oracle Fusion Middleware, Oracle E-Business Suite, Oracle Supply Chain, Oracle PeopleSoft, Oracle JD Edwards, Oracle Siebel CRM, Oracle Communications Applications, Oracle Retail Applications, Oracle Health Sciences Applications and Oracle Financial Services. Other product groups could be indirectly impacted depending on the implementation details, the infrastructure and the components supporting the deployment of each Business Critical Application. For example, if Oracle E-Business Suite is running on top of an Oracle Database, the exposure of the EBS could be increased, as vulnerabilities related to the Database could also affect the business data.
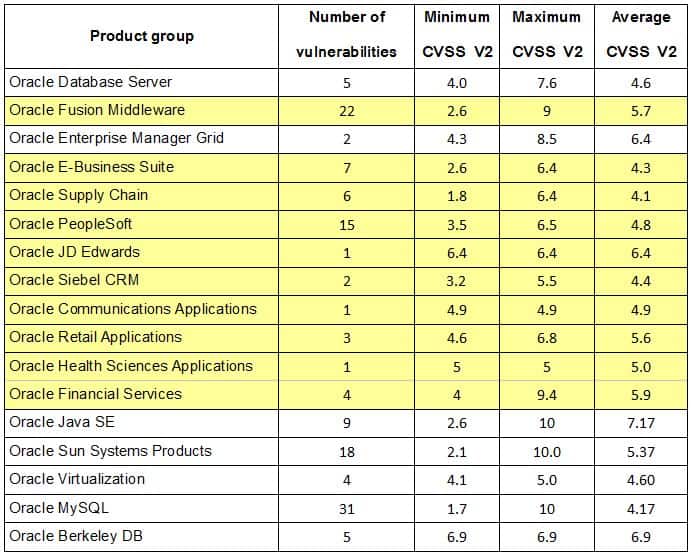
The top 3 affected product groups are: Oracle MySQL, Oracle Fusion Middleware and Oracle Sun Systems Products. In the last Critical Patch Updates released by Oracle, its Fusion Middleware solution was also placed among the top 3 affected product groups, meaning that most of the fixed were issued for vulnerabilities affecting that product.
The following table shows the number of vulnerabilities published for each product group, according to the April 2016 Oracle CPU:
While it is important to identify the CVSS of the vulnerabilities, the distribution of the CVSS risks in context to all vulnerabilities patched by Oracle for this CPU is also important.
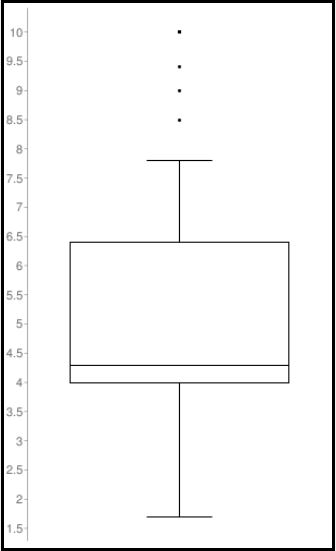
The box plot graph illustrates the distribution of CVSS V2 scores across the April 2016 Oracle Critical Patch Update. As represented in the graph, the CVSS V2 range values go from 1.7 to 10.0 with a median of 5.
There are seven vulnerabilities with a CVSS V2 score of 10, which due to the number of vulnerabilities being patched, does not affect the median, but definitely requires special consideration as they are comprised of a variety of critical vulnerabilities. Four of these affect Oracle Java SE product group (CVE-2016-3443, CVE-2016-0687, CVE-2016-0686 and CVE-2016-3427). Another vulnerability with a CVSS V2 score of 10 affects Oracle Sun Systems (CVE-2016-0693).
It is very important to understand that a CVSS score of 10 implies that confidentiality, integrity and availability can be completely compromised through the exploitation of these vulnerabilities. It is also important to note that most business critical applications use Java with Web-based content and enterprise software components in Java. Oracle published that 97% of Enterprise Desktops Run Java.
Vulnerabilities with CVSS 10
- CVE-2016-3443; 10 (AV:N/AC:L/Au:N/C:C/I:C/A:C): Java SE 2D component allows a remote attacker to execute remote exploits without authentication which affects confidentiality, integrity and availability.
- CVE-2016-0687; 10 (AV:N/AC:L/Au:N/C:C/I:C/A:C): Java SE and Java SE Embedded component with subcomponent Hotspot allows a remote attacker to execute remote exploits without authentication which affects confidentiality, integrity and availability.
- CVE-2016-0686; 10 (AV:N/AC:L/Au:N/C:C/I:C/A:C): Java SE and Java SE Embedded component with subcomponent Serialization allows a remote attacker to execute remote exploits without authentication which affects confidentiality, integrity and availability.
- CVE-2016-3427; 10 (AV:N/AC:L/Au:N/C:C/I:C/A:C): Java SE, Java SE Embedded and Jrockit component with JMX subcomponent allows a remote attacker to execute remote exploits without authentication which affects confidentiality, integrity and availability.
- CVE-2016-0693; 10 (AV:N/AC:L/Au:N/C:C/I:C/A:C): Solaris component with PAM LDAP module allows a remote attacker to execute remote exploits without authentication which affects confidentiality, integrity and availability.
The Oracle Critical Patch Updates CVSS V3 are available for at:
http://www.oracle.com/technetwork/security-advisory/cpuapr2016v3-2985753…
The Oracle Critical Patch Updates CVSS V2 are available for at:
http://www.oracle.com/technetwork/topics/security/cpuapr2016-2881694.html
Stay tuned for our upcoming Oracle Critical Security Update’s scheduled for:
- July 19, 2016
- October 18, 2016
- January 17, 2017
- April, 18 2017



