DORA Enforcement in 2026: What the Regulation Means for SAP Landscapes

The Digital Operational Resilience Act (DORA) fundamentally shifted the regulatory landscape for the European financial sector when active enforcement began in January 2025. Moving into 2026, regulators expect comprehensive, real-time evidence of operational resilience rather than theoretical governance. For organizations operating complex enterprise environments, aligning this framework with a broader SAP Governance, Risk, and Compliance (GRC) strategy is an immediate operational imperative.
This overview defines DORA for financial entities and ICT providers, details the severe non-compliance penalties, and explicitly outlines why SAP systems fall directly under the regulatory umbrella.
The 2026 Regulatory Reality for Digital Operational Resilience
The informal tolerance period for DORA compliance has ended, with regulatory authorities now demanding practical effectiveness of Information and Communication Technology (ICT) controls under the threat of severe financial penalties.
Regulators evaluate the practical effectiveness of an organization’s defensive posture, incident reporting speed, and continuous vulnerability management. Non-compliance carries devastating consequences. Entities found violating DORA provisions face severe financial penalties, with fines reaching up to 2% of a company’s global annual turnover. Regulatory bodies also possess the authority to impose public notices, cease-and-desist orders, and operational restrictions on non-compliant institutions.
Securing the “Crown Jewels”: Why SAP is a Primary DORA Target
Because DORA mandates the rigorous protection of “Critical or Important Functions,” the SAP landscape is a primary regulatory target due to its role as the operational engine for financial data, procurement, and human resources.
DORA requires organizations to secure the systems necessary for the continuous functioning of the financial sector. Because SAP houses an organization’s most sensitive data and executes its most critical business processes, a disruption at the SAP application layer inherently triggers systemic operational failure. Threat actors specifically target ERP systems to bypass standard network perimeters, hijack administrative privileges, and execute unauthorized financial transactions. Protecting these environments requires continuous vulnerability management and real-time threat detection to satisfy regulatory expectations.
SAP’s Designation as a Critical ICT Third-Party Service Provider (CTPP)
The European Supervisory Authorities (ESAs) officially designated SAP as a Critical ICT Third-Party Service Provider (CTPP) in November 2025, elevating the regulatory oversight and shared responsibility for enterprise customers.
This designation recognizes SAP’s essential role in supporting the digital infrastructure of the global financial sector. As a CTPP, SAP is subject to direct oversight by the ESAs to ensure enhanced operational resilience. For enterprise customers and financial institutions, this designation heavily impacts the shared responsibility model and third-party risk management strategies. While SAP is responsible for the security of the cloud infrastructure, individual organizations remain entirely accountable for securing the configurations, custom code, and user authorizations residing within their specific SAP environments.
The Five Core Pillars of DORA Compliance
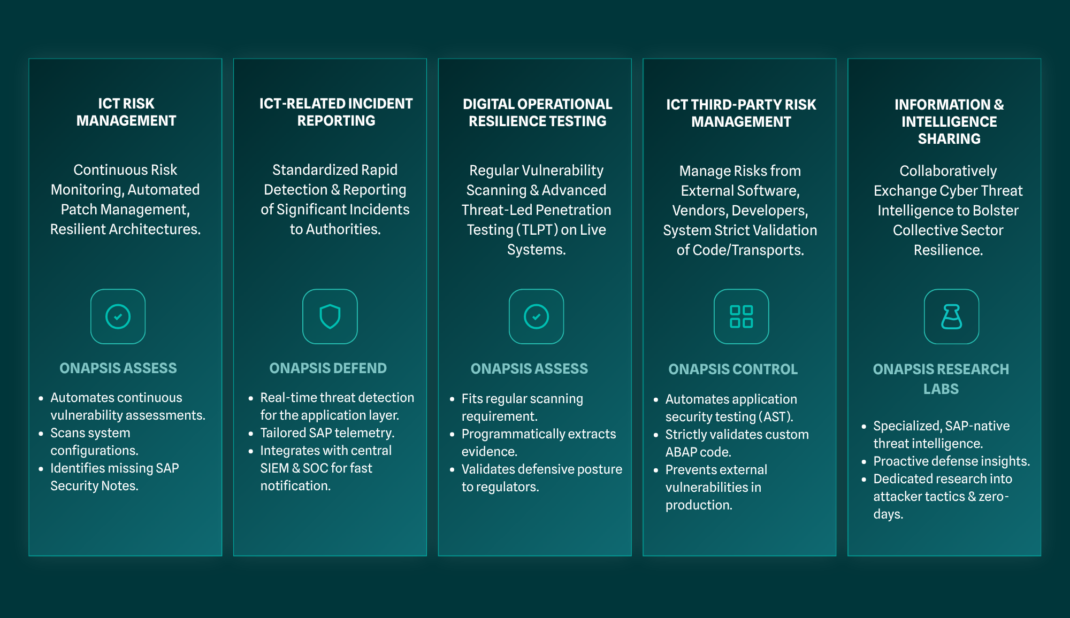
DORA establishes a universal framework built upon five core pillars designed to ensure financial entities can withstand, respond to, and recover from severe cyberattacks.
To achieve compliance, organizations must map their SAP security capabilities directly against these five foundational requirements:
- ICT Risk Management: Establishing robust, continuous frameworks to identify vulnerabilities, protect against cyber threats, and enforce secure system configurations.
- ICT-Related Incident Reporting: Standardizing rapid detection and reporting protocols for significant cyber incidents, requiring seamless integration between SAP telemetry and corporate Security Information and Event Management (SIEM) tools.
- Digital Operational Resilience Testing: Mandating regular vulnerability scanning and advanced Threat-Led Penetration Testing (TLPT) on live production systems to validate defensive capabilities.
- ICT Third-Party Risk Management: Managing the operational risks introduced by external vendors, software providers, and system integrators, necessitating strict validation of custom code and transports.
- Information Sharing: Encouraging financial entities to collaboratively and securely exchange cyber threat intelligence to bolster the collective resilience of the European financial sector.
Automating SAP Compliance Audits for DORA
Transitioning from manual, point-in-time audits to continuous compliance automation is a strategic imperative for satisfying stringent regulatory reporting and risk management requirements.
Traditional manual audits often introduce significant security blind spots by providing only a static snapshot of an organization’s security posture. In alignment with DORA mandates, regulators require continuous operational resilience. The Onapsis platform facilitates the establishment of a continuous, audit-ready state, ensuring that SAP configurations and user authorizations maintain real-time compliance. This continuous adherence is achieved through the implementation of Continuous Controls Monitoring (CCM).
By automating SAP compliance audits, organizations eliminate manual evidence collection, gaining real-time visibility into system configurations, user authorizations, and Segregation of Duties (SoD) conflicts.
The Onapsis Platform operationalizes this continuous monitoring model. Solutions like Onapsis Assess, paired with Onapsis Comply add-on packs, automate complex auditing and evidence collection.
While financial entities adapt to the new DORA mandates, leveraging these existing out-of-the-box compliance checks for rigorous, parallel standards like NIS2, NIST, and GDPR establishes the foundational vulnerability management and configuration governance required for operational resilience. This automation programmatically extracts technical evidence and generates audit-ready reporting, allowing security teams to identify and remediate vulnerabilities before they escalate into compliance violations or systemic breaches.
Frequently Asked Questions
What entities fall under the scope of DORA compliance?
The Digital Operational Resilience Act applies to all financial entities operating within the European Union, as well as their critical Information and Communication Technology (ICT) third-party service providers. This includes banks, investment firms, insurance companies, crypto-asset providers, and software vendors like SAP that provide essential infrastructure to the financial sector.
Why was SAP designated as a Critical ICT Third-Party Service Provider (CTPP)?
European Supervisory Authorities (ESAs) designated SAP as a CTPP because its enterprise resource planning (ERP) platforms form the foundational infrastructure for global financial institutions. A disruption to SAP services poses a systemic risk to the European financial sector, necessitating direct regulatory oversight and enhanced operational resilience standards.
What are the financial penalties for DORA non-compliance?
Organizations failing to comply with DORA requirements face severe financial penalties reaching up to 2% of their global annual turnover. Regulatory authorities also hold the power to issue public notices, mandate remediation efforts, and impose operational restrictions on non-compliant financial entities and ICT providers.
When did active enforcement of the Digital Operational Resilience Act begin?
Active regulatory enforcement of DORA officially began on January 17, 2025, marking the end of the formal implementation period. Regulators now expect financial institutions to provide practical, real-time evidence of their operational resilience, threat-led penetration testing, and continuous vulnerability management capabilities.
How does DORA specifically impact SAP security requirements?
DORA requires organizations to shift from theoretical compliance to active threat detection and continuous vulnerability management within their SAP landscapes. Security teams must automate configuration monitoring, secure custom code development, and integrate SAP threat telemetry directly into corporate incident reporting protocols to meet stringent regulatory thresholds.
