Onapsis
Onapsis protects the business-critical applications that run the global economy. As the market leader in ERP cybersecurity, we provide the most comprehensive solution for securing SAP and Oracle applications. Our threat intelligence is powered by the Onapsis Research Labs, the world’s leading team of SAP security researchers dedicated to uncovering critical vulnerabilities and threats affecting mission-critical systems.

The Utilities Guide to SAP RISE: Navigating Shared Responsibility and Security
Electric utilities operate in a highly regulated physical domain. As organizations like Oklahoma Gas and Electric (OG&E) modernize their enterprise resource planning environments, executing a secure RISE with SAP business transformation requires a fundamental shift in defensive strategy. Defending the enterprise core requires security leaders to understand that migrating to a hyperscaler does not eliminate…

Securing the SAP Core of Global Luxury: A 2026 Threat Briefing
Discover why SAP vulnerabilities pose a critical risk to luxury brand equity and how organizations can protect UHNW client data from advanced cyber threats.

The Business Benefits of RISE with SAP: Don’t Overlook Security
RISE with SAP is a commercial transformation that bundles a modern ERP core, innovation tools, and process intelligence into a single service. Its true business value is not in the contract itself, but in the specific financial levers it unlocks: reducing Total Cost of Ownership (TCO) via a “Clean Core,” accelerating innovation revenue via SAP…
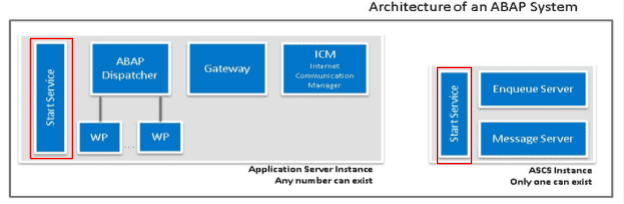
SAP Management Console: Concepts, Architecture, and Security Hardening
The SAP Management Console (SAP MC) provides a common framework for centralized system management. It allows you to monitor and perform basic administration tasks on the SAP system centrally, which simplifies system administration.
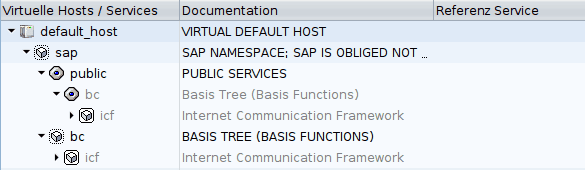
Introducing SAP ICF Services: Concepts and General Considerations
The purpose of this blogpost is to introduce Internet Communication Framework services, also known as ICF services.
Digitalisierung Ist Kein Spaziergang—Jedoch Eine Chance!
Steffen Pietsch, DSAG-Vorstand Technologie, eröffnete die diesjährigen DSAG-Technologietage mit einer sehr lebendigen und kritischen Keynote.
Tipps zur Absicherung von Cloud-ERP-Systemen
„Die betrügerischen Zwölf“ („The Treacherous 12“) nennt die Cloud Security Alliance (CSA) die größten Sicherheitsrisiken für Daten in der Cloud – und fasst in einem neuen Whitepaper die wichtigsten Steuerungen und Kontrollen zusammen, um Cloud-ERP-Kunden bei der Abwehr dieser Top-Bedrohungen zu unterstützen.
Video: Automate the Audit
As regulatory changes are made every year and audit fatigue becomes the norm, the cost to protect your organization and avoid audit violations and fines continues to rise.
Video: Change Assurance
If you’re like 81% of the CIOs and CISOs recently surveyed, your team has held off on making these changes due to concerns about impact on business performance, while at the same time being under massive pressure to support business growth.
