Attack & Secure SAP Systems with Onapsis Research Labs at Troopers Conference

We are very happy to announce that Onapsis Research Labs’ renowned SAP Security Training “Attack & Secure SAP: 2022 Edition” has been once again accepted at Troopers.de Conference on June 27-28, 2022.
In this two day training, students will have the opportunity to learn not only how to assess the security of your most critical systems by performing tailored penetration testing, but also how to secure and monitor systems from the latest threats. The training is highly practical, which means that students will spend most of the session doing hands-on exercises.
The training covers a wide range of topics from the basics of SAP architecture and how to identify components to advance exploitation to post-exploitation scenarios and how to protect systems against these threats. Some of the topics that attendees will study include:
- SAP systems discovery and mapping (reconnaissance) using common industry techniques but also specific SAP trickery
- How to exploit known vulnerabilities and misconfiguration and how to protect against these threats
- Post-exploitation and lateral movement techniques
- Which tools and data sources are provided by SAP in order to perform forensic assessments and how to use them
- And so much more…
If you’re interested in learning about some of the most recent techniques that attackers are using to compromise SAP Applications or performing lateral movement in SAP environments (“What should we expect attackers to do after an initial compromise such as exploiting RECON?“) and how to secure them, then this training is for you!
Here are some examples of the content and challenges training goes through:
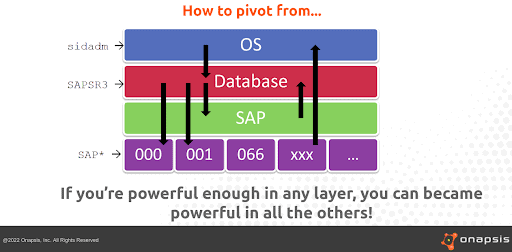
Extract of the training, highlighting lateral movement
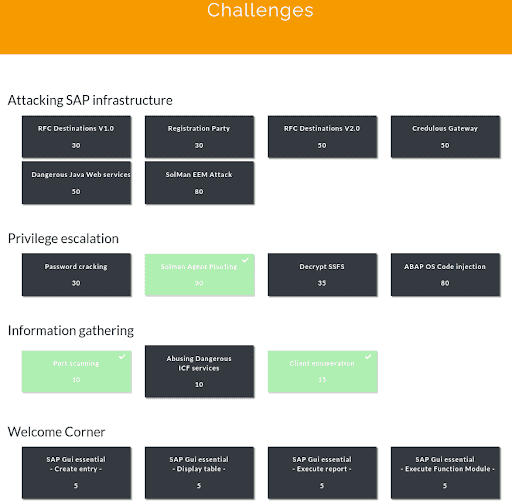
Example of the challenges of the training
All the training architecture required in order to carry out the practical lessons will be provided and hosted by Onapsis’ own servers. All students need to bring is a laptop with a SSH connection, SAP GUI installed, and a willingness to roll up their sleeves and learn!
Onapsis’s Yvan Genuer will also be hosting a session on SAP Focused Run, the brand new product in the SAP world, a spin off of SAP Solution Manager. This talk will describe Onapsis Research Labs’ journey assessing this component, what we found, and why it is critically important to assess and monitor all the SAP landscape.
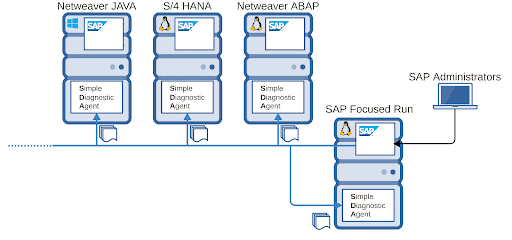
A simple SAP Landscape connected to SAP Focused Run
Don’t miss the chance of attending one of the best conferences and get trained by Onapsis Research Labs experts. We’ll see you in Heidelberg!
