Analyzing SAP Security Notes May 2016
SAP systems run an organization’s mission-critical processes, and house an organization’s most sensitive data. Because of this, it is critical that these systems receive the proper security they deserve. This security begins with closing the gap of software vulnerabilities by applying security patches released by SAP in a timely manor.
SAP systems differ from traditional web applications and even operating systems due to their complexity which is caused by customized changes introduced in customer implementations, to better suit business needs (a.k.a. customizations). These customizations can sometimes make it difficult to identify whether a patch has been properly applied to ensure that newly disclosed vulnerabilities are mitigated.
In order to provide a predictable and scheduled flow of vulnerability mitigation information and security patches, SAP releases the major part of their latest Security Notes information on the second Tuesday of every month. Due to this regular disclosure of new security issues that could potentially weaken the security of SAP systems within an organization, it’s highly recommended to carry out periodic assessments on at minimum, a monthly basis.
At Onapsis, we are very concerned about the security of our client’s SAP systems. To better assist our customers, we perform a detailed analysis of the monthly SAP Security Notes, as soon as they are published by SAP. The goal of this is to provide SAP clients with detailed information about each release of new security patches which fix vulnerabilities affecting their SAP systems and help guide testing of these systems within the organization.
Between the last published SAP Security Tuesday and today, 20 new SAP Security notes were published by SAP (taking into account 10 Support Packages and 10 Patch Day Notes).
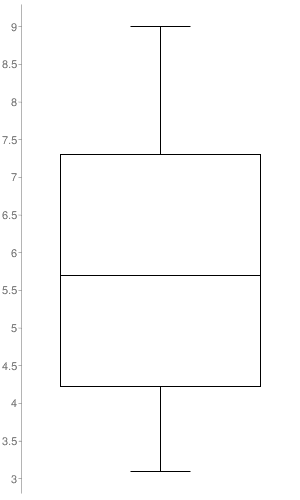
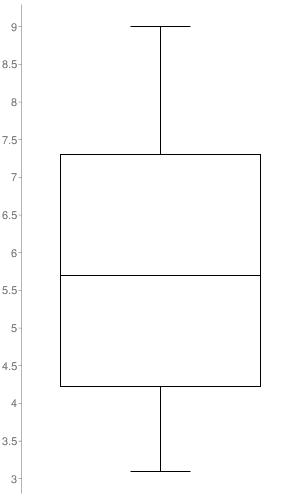
The box-plot graph illustrates the distribution of CVSS v3 scores across the Security Notes released. The only notes taken into account were the ones in which SAP set a CVSS v3 (10 out of the 20 SAP Security Notes). As represented in the graph, the SAP Security Notes range values go from 3.1 to 9.0 with a median of 5.7.
Hot News from SAP
- 2296023 – 9.0 (AV:N/AC:H/PR:N/UI:N/S:C/C:H/I:H/A:H). Missing Authentication check in SAP ASE XPServer. Under certain circunstances, the XPServer could be abused by an attacker, allowing the unauthenticated user to execute arbitrary command execution in the server running the SAP ASE.
SAP Security Notes with higher CVSS scoring provided by SAP
- 2307384 and 2298367 – 7.3 (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L). SAP Predictive Analytics and Crystal Reports for Enterprise were using a version of Apache Commons Collections, which deserializes untrusted data without sanitizing it properly. This could allow a malicious user to execute arbitrary commands in the remote server.
Other corrections with High Priority (no CVSS provided by SAP)
- 2195409: Potential modif./disclosure of persisted data in SAP CPQ Solution Configuration (SME). The component SAP CPQ Solution Configuration was vulnerable to an SQL injection attack; by exploiting it, an attacker may modify data into the database or retrieve information from the database.
- 1850010: Potential modif./disclosure of persisted data in CRM-CM. The component SAP CRM Case Management was vulnerable to an SQL injection attack; by exploiting this vulnerability, an attacker may modify data into the database of the product or retrieve information from the database.
- 1933375: RU ERP for Banking. Missing authorization check. Potential modification of persisted data. This note fixes a security bug in the components Financial Accounting and Localization for Russia. Both components lack of proper authentication checking, thus an authenticated user may use functions of these two modules to which access should be restricted.
Other attack vectors
- Reflected Cross-site Scripting (XSS): Notes 2260876, 2289575, 2300197
- Information disclosure: Notes 2297853, 2281002, 2296722
- Missing authority check: Notes 2051717, 2043447, 2201916, 2298657
- Hardcoded value: Note 2292487
- Spreadsheet formula injection: Note 2272676
- Information about a security parameter configuration: Note 1444282
- Clickjacking vulnerability: Note 2254425
Each month Onapsis updates its flagship product Onapsis Security Platform (OSP) to allow you to check whether your systems are up to date with these latest SAP Security Notes as well as ensuring those systems are configured with the appropriate level of security to meet your audit and compliance requirements.
Stay tuned for next month’s Security Notes analysis from the Onapsis Research Labs.
NOTE:
SAP published their monthly post in their SCN space “The Official SAP Product Security Response Space”, providing information about the SAP Security Notes. Here it’s the link to the SAP blogpost: “SAP Security Patch Day – May 2016”

