Analyzing SAP Security Notes April 2016
SAP is a complex and ever changing system, whether because of changes introduced to your SAP implementation to better suit your business or through the application of Security Notes (Patches) to ensure that newly disclosed vulnerabilities are mitigated.
In order to provide a predictable and scheduled flow of vulnerability mitigation information and security patches, SAP releases the major part of their latest Security Notes information on the second Tuesday of every month. Due to this regular disclosure of new security issues that could potentially weaken the security of SAP systems within an organization, it’s highly recommended to carry out periodic assessments on a monthly basis at least.
At Onapsis we are very concerned about our client’s SAP system security and also the state of SAP security in general, so to assist our customers, we perform a detailed analysis of the monthly SAP Security Notes as soon as they are published. The goal of this is to provide SAP clients with detailed information about the newly released notes and vulnerabilities affecting their SAP systems and help guide their testing of these systems within their organization.
Between the last published SAP Security Tuesday and today, there were 26 SAP Security notes published by SAP AG (taking into account 7 Support Packages and 19 Patch Day Notes). The Onapsis Research Labs contributed to reporting these vulnerabilities found in the SAP Software (Acknowledgments to Security Researchers).
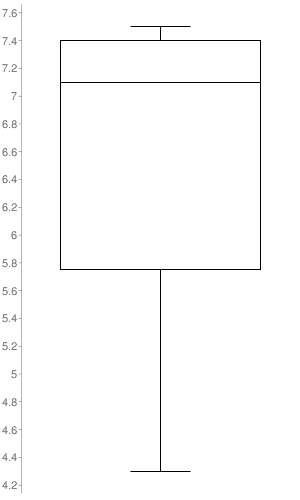
The box-plot graph illustrates the distribution of CVSS scores across the Security Notes released. The only notes taken into account to build it, were the ones to which SAP set a CVSS score (17 out of the 26 SAP Security Notes). As it’s represented in the graph, the SAP Security Notes range values go from 4.3 to 7.5 with a median of 7.1.

SAP Security notes released for vulnerabilities reported by Onapsis:
- 2262710– Denial of service (DOS) vulnerability in HANA DP Agent. 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H). It is possible to perform an unauthenticated Denial of Service in the HANA Data Provisioning agent rendering it unavailable until the next process restart.
- 2280054 – Information Disclosure in Data Provisioning Agent. 5.3 (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N). The SAP HANA DP agent could allow remote unauthenticated attackers to obtain sensitive information of the target platform.
- 2262742 – Missing Authentication check in HANA DP Agent. 7.3 (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L). Certain administrative functions in the SAP HANA DP agent doesn’t require authentication to be used.
- 2274560 – Arbitrary Log File Injection vulnerability in SAP Gateway. 7.3 (AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N). The SAP Gateway is prone to log injection attacks when specially crafted RFC packets are used.
Other corrections with high priority:
- 2254389 – XXE vulnerability in SAP UDDI (Universal Description, Discovery and Integration) 7.1 (AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:N/A:H). Untrusted XML input parsing is possible in SAP UDDI (Universal Description, Discovery and Integration). The note fixes an XML eXternal Entity type vulnerability, through which a malicious user may send a specially crafted XML content to perform a Denial of Service or retrieve data from the affected SAP System.
- 2252191 – Deserialization of untrusted data in SAP HANA XS Advanced Java Runtime 7.3 (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L). The affected component deserializes untrusted data without any prior input sanitization. This could lead to Remote DoS attacks or Remote command execution.
- 2294689 – SQL Injection vulnerability in SAP ASE 7.2 (AV:N/AC:L/PR:H/UI:N/S:H/C:H/I:L/A:H). This note fixes an authenticated SQL injection in SAP ASE (Adaptive Server Enterprise). This could allow remote authenticated attackers to execute arbitrary queries over the database.
- 2265514 – Deserialization of untrusted data in Groovy Engine 7.3 (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L). SAP Mobile Platform uses a vulnerable version of Apache Groovy to CVE-2015-3253. This note fixes this issue.
- 2300197 – Cross-Site Scripting (XSS) vulnerability in SAP Solution Manager Fiori Apps ‘My Incidents’ and ‘My Business Requirements’. This note fixes different XSS attacks in ‘My Incidents’ and ‘My Business Requirements’ applications. Reflected Cross-Site Scripting attacks could allow attackers to change information on a non-permanent way or to steal credentials from valid users.
- 2256185 – Potential denial of service in SAP Internet Communication Manager 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H). This note fixes a potential unauthenticated DoS attack against the SAP Internet Communication Manager.
- 2259547 – Potential denial of service in jstart 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H) This note fixes a potential unauthenticated DoS attack against the Java Startup Framework.
Types of vulnerabilities fixed this month:
- Reflected Cross-site Scripting (XSS): Notes 2201295, 2274286, 2273241, 2263719
- Missing and Switchable authority checks: Notes 2267789, 2297003, 1951340, 2281095, 1943280, 2213128
- Clickjacking attacks: Note 2244161
Each month Onapsis updates its flagship product Onapsis Security Platform (OSP) to allow you to check whether your systems are up to date with these latest SAP Security Notes as well as ensuring those systems are configured with the appropriate level of security to meet your audit and compliance requirements.
Stay tuned for next month’s Security Notes analysis from the Onapsis Research Labs.

