Inside Our Q1 2026 Feature Release: Empowering Teams with Granular Control and Intelligent Automation
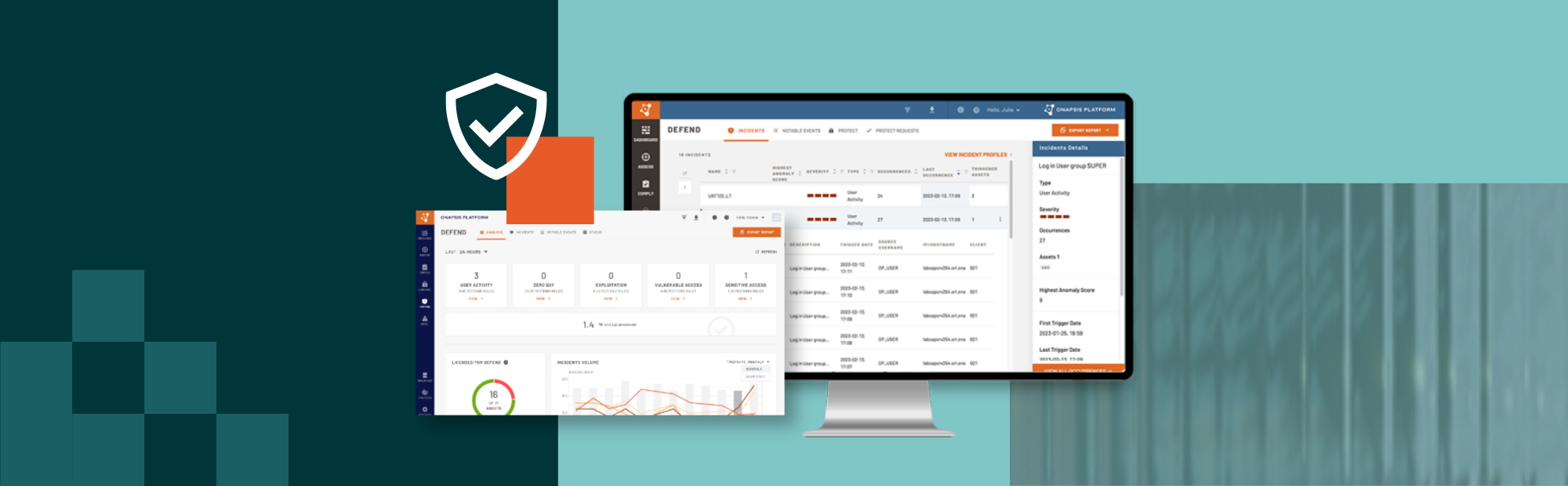
Your security is our priority. This Q1, we’re launching new, high-impact features designed to streamline your SAP cyber defense and provide the industry’s most proactive protection.
At a Glance: Q1 2026 Release Highlights
- New enhanced customization capabilities to tailor your defense, eliminate manual efforts, and focus efforts on what matters most to your business
- Next wave of Rapid Controls for Onapsis Defend focused on overly privileged users
- Extended transport guard with new application security testing for SAP cTMS, enabling automated and secure transport of custom code
As the only SAP Endorsed App for cybersecurity, Onapsis remains deeply committed to securing the world’s most business-critical landscapes. This Q1, we are doubling down on that mission by launching new, high-impact features designed to bridge the gap between sophisticated threat protection and operational efficiency. From intelligent automation that streamlines compliance to granular controls that allow for a perfectly tailored security posture, our latest innovations ensure your modern SAP environment remains resilient, compliant, and agile in an evolving threat landscape.
To help you stay ahead of evolving threats while reducing manual overhead, our latest release focuses on three key themes:
- Expanded Platform Customization: Tailor your defense with granular access controls, flexible out-of-the-box vulnerability scans, and focused event muting to align perfectly with your unique security posture.
- Proactive Threat Defense: Protect against internal risks with specialized Rapid Controls designed to identify and mitigate overly privileged users.
- Unified Transport Governance: Streamline compliance and change management through seamless SAP cTMS integration, enforcing automated security guards across your entire transport pipeline
Enhanced Platform Customization in Onapsis Assess and Defend
These customization updates are all about making it easier to tailor Onapsis solutions to fit your needs and were inspired by direct feedback from our customers. The new features allow you to reduce manual efforts and focus your resources on the high-impact vulnerabilities and threats that truly matter to your specific security posture.
- Additional access controls for the Onapsis Platform: Enable broader team collaboration within Onapsis solutions, ensuring users have the visibility they need without compromising security or violating least privilege principles.
- Streamlined vulnerability scan optimization in Assess: We’ve always offered the flexibility of custom scans and checks. Now, we’re making that precision effortless. By modifying baseline policies directly, you can ensure vulnerability scans are laser-focused on your environment without maintenance overhead.
- Intelligent event tuning in Defend: Allow your team to focus on their efforts on what matters most to your organization and security posture by instantly muting lower priority activities detected in SAP application logs (e.g., known-safe activity on DEV systems).
Proactive Threat Defense – Onapsis Defend Rapid Controls for Over-Privileged Users
Following the successful Q3 ’25 launch of exploit-based compensating controls, our latest wave of Defend Rapid Controls shifts the focus from external vulnerabilities to internal risk management. While the first phase allowed customers to immediately monitor for exploit activity targeting unpatched vulnerabilities, this new release addresses the risk of over-privileged or “super users”.
When Onapsis Assess identifies highly privileged or default accounts within your landscape, you can now instantly deploy a compensating control in Onapsis Defend to monitor and alert on subsequent, potentially suspicious user activity related to those accounts. For example, if Assess identifies that a default, highly privileged user is active on a system, with the click of a button, you can have Defend start alerting on logins of that user to inform and accelerate incident response.
Unified Transport Governance – New SAP cTMS Integration for Onapsis Control
Building on our proven transport security for the classic SAP TMS, we are extending our protection to the SAP Business Technology Platform (BTP). This ensures that every change, whether within your on-premises core or on the path to the cloud, is governed by the same rigorous security standards. By providing an enhanced transport guard, Onapsis Control ensures that change management always maintains compliance and system integrity, regardless of which transport service is in use.
This new integration allows for automated security validation directly within SAP cTMS import queues and serves as the foundation for security within SAP Cloud ALM. By scanning ABAP Cloud transports before they are deployed, you can identify and block critical vulnerabilities in real time, preventing risky code from ever reaching your production environments. This proactive approach ensures that your cloud-native developments meet the highest security standards from day one, identifying unauthorized access patterns and compliance violations before they can impact your business.
Availability
All features mentioned here will reach general availability (GA) by the end of Q1 2026. Exact GA release dates may vary based on product, capabilities, and release cadence. Contact an Onapsis sales representative or authorized systems integrator for pricing and further details.

