SAPStartSrv – Pre-auth buffer overflow
Impact On Business
- If parameter service/localconnection = compat :
- If parameter service/localconnection is not set :
- Both scenarios lead to fully compromising all different SAP Systems running on the target host.
Vulnerability Details
The SAP Start Service, listening on port 1128 (http) and 1129 (https) allow unauthenticated users to access several SOAP methods under namespace SAPOsCol. Two of them, SendRequestAsync and SendRequest, don’t correctly handle the parameter name when a specific request ID number is called. Indeed a memory corruption vulnerability, Stack Based Buffer Overflow, exists on saposcol binary through this method call.- The crash appears during a ret mnemonic with controlled RSP registry.
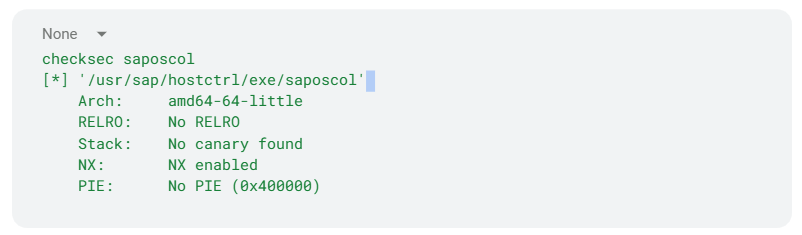
- Only the security feature NX is enable for this saposcol version:
- It is possible to leak the libc version using the SOAP method GetHwConfText
- Using the same method GetHwConfText, it is also possible to bypass ASLR because the result leaks the current RIP address of running saposcol binary.
Solution
SAP has released SAP Note 3275727 which provides patched versions of the affected components. The patches can be downloaded from https://me.sap.com/notes/3285757. Onapsis strongly recommends SAP customers to download the related security fixes and apply them to the affected components in order to reduce business risks.Report Timeline
- 11/21/2022: Onapsis sends details to SAP
- 11/30/2022: SAP asks for clarification
- 12/01/2022: Onapsis provide more explanation
- 12/07/2022: SAP asks for clarification
- 12/08/2022: Onapsis provide more explanation
- 02/24/2023: SAP decrease the CVSS score
- 03/14/2023: SAP releases SAP Note fixing the issue
References
- Onapsis blogpost: https://onapsis.com/blog/sap-patch-day-march-2023/
- CVE Mitre: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-27498
- Vendor Patch: https://me.sap.com/notes/3275727
- Hack In The Box, Phuket, 2023 A Story Of Unexpected Intrusion Testing Results https://www.youtube.com/watch?v=jkSaP_KH-yY
Advisory Information
- Public Release Date: 07/23/25
- Security Advisory ID: ONAPSIS-2024-0017
- Researcher(s): Yvan Genuer
Vulnerability Information
- Vendor: SAP
- Affected Components: SAP Host Agent
- SAPHOSTAGENT 7.22 SP058 and lower (Check SAP Note 3275727 for detailed information on affected releases)
- Vulnerability Class: CWE-121
- CVSS v3 score: 9.0 AV:N/AC:H/PR:N/UI:N/S:C/C:H/I:H/A:H
- Risk Level: Critical
- Assigned CVE: CVE-2023-27498
- Vendor patch Information: SAP Security NOTE 3275727
