SAP Security Notes: April 2026 Patch Day
HotNews Note published: Onapsis Research Labs supported SAP in patching a critical SQL Injection vulnerability
Highlights of April SAP Security Notes analysis include:
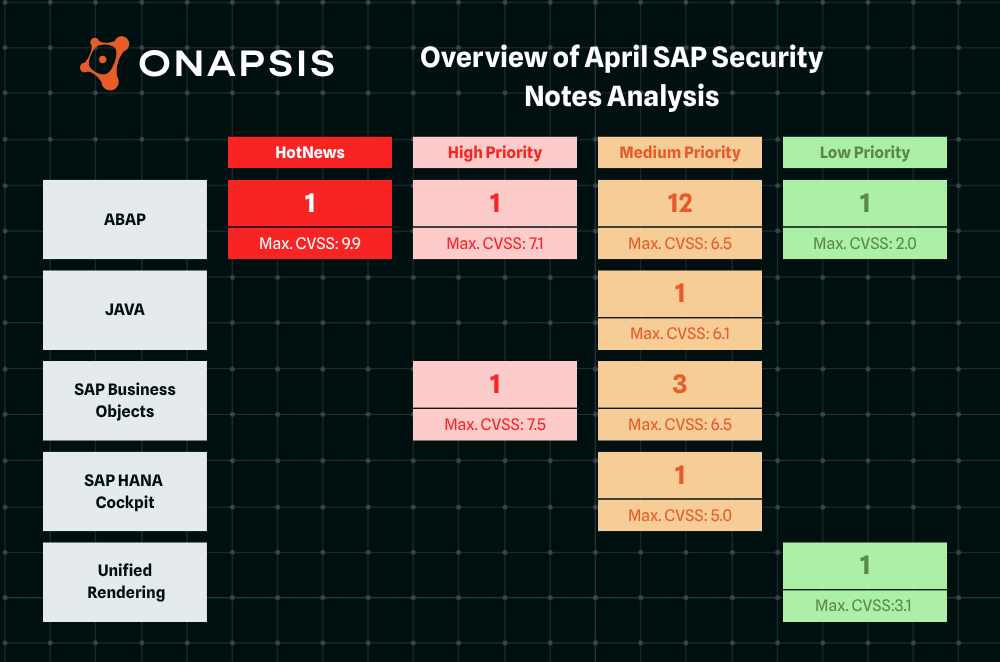
- April Summary – Twenty-two new and updated SAP security patches released, including one HotNews Note and two High Priority Notes
- SQL Injection vulnerability – CVSS 9.9 vulnerability in SAP Business Planning and Consolidation and SAP Business Warehouse requires immediate patching
- Onapsis Research Labs Contribution – Our team supported SAP in patching six vulnerabilities, covered by five SAP Security Notes, including one HotNews Note
SAP has published twenty-two new and updated SAP Security Notes in its April Patch Day, including one HotNews Note and two High Priority Notes. Five of the eighteen new SAP Security Notes were published in collaboration with the Onapsis Research Labs.
The HotNews Notes in Detail
The Onapsis Research Labs (ORL) supported SAP in patching a critical SQL Injection vulnerability in SAP Business Planning and Consolidation and SAP Business Warehouse. The vulnerable ABAP program allows a low privileged user to upload a file with arbitrary SQL statements that will then be executed. SAP Security Note #3719353, tagged with a CVSS score of 9.9, patches the vulnerability by deactivating all executable code within the affected program. As a temporary workaround, SAP recommends revoking the S_GUI authorization object with Activity 60 (Upload) from user accounts. Since this workaround can lead to side effects for the affected users in other applications and because of the criticality of the vulnerability, we strongly recommend applying the patch immediately.
The High Priority Notes in Detail
SAP Security Note #3678282, tagged with a CVSS score of 7.5, was initially released in February 2026 and patches a Denial of Service vulnerability in SAP BusinessObjects BI Platform that was previously reported to SAP by the Onapsis Research Labs. The update only provides a minor correction to the ‘Symptom’ section of the note.
SAP Security Note #3731908, tagged with a CVSS score of 7.1, patches a Missing Authorization check vulnerability in SAP ERP and SAP S/4 HANA (Private Cloud and On-Premise). The vulnerability allows an authenticated attacker to execute a particular ABAP program to overwrite any existing eight‑character executable program without authorization. According to SAP, a successful exploitation impacts availability, with a limited impact on integrity confined to the affected report, while confidentiality remains unaffected.
Onapsis Contribution
In addition to HotNews Note #3719353, the Onapsis Research Labs (ORL) supported SAP in patching five Medium Priority vulnerabilities, covered by four SAP Security Notes.
SAP Security Note #3705094, tagged with a CVSS score of 6.5, describes a vulnerability that poses the confidentiality of the application at high risk. Certain remote-enabled function modules in SAP Business Analytics and SAP Content Management allow an authenticated user accessing sensitive information beyond their intended permissions. After patching, the vulnerable function modules are no longer accessible remotely.
SAP Security Note #3692004, tagged with a CVSS score of 6.1, patches an Open Redirect vulnerability in SAP NetWeaver AS ABAP. The ORL team detected that an unauthenticated attacker could craft malicious URLs that, if accessed by a victim, could be redirected to the page controlled by the attacker. To avoid problems after patching, it might be necessary to extend the allow list in Unified Connectivity (UCON) or table HTTP_WHITELIST in older SAP releases without UCON.
SAP Security Note #3645228, tagged with a CVSS score of 6.1, addresses two vulnerabilities that can lead to Cross-Site Scripting in SAP Supplier Relationship Management (SICF Handler in SRM Catalog). The vulnerable ICF service allows an unauthenticated attacker to craft a malicious URL that, if accessed by a victim, results in execution of malicious content within the victim’s browser. This could allow the attacker to access and modify information, impacting the confidentiality and integrity of the application, while availability remains unaffected.
SAP Security Note #3703276, tagged with a CVSS score of 4.3, patches a Missing Authorization Check vulnerability in the Material Master application. Our team detected that a remote-enabled function module of the application does not perform sufficient authorization checks before accessing sensitive information.The vulnerability has a low impact on confidentiality and does not affect integrity and availability of the system.
Summary & Conclusions
With twenty-two SAP Security Notes, including one HotNews Note and two High Priority Notes, SAP’s April Patch Day is another busy one. The relatively low number of HotNews and High Priority Notes should not prevent you from carefully checking each and every SAP Security Note. We are proud that our Onapsis Research Labs team could once more significantly contribute to making SAP more secure.
| SAP Note | Type | Description | Priority | CVSS |
| 3719353 | New | [CVE-2026-27681] SQL Injection vulnerability in SAP Business Planning and Consolidation and SAP Business Warehouse EPM-BPC-NW-SQE | HotNews | 9.9 |
| 3678282 | Update | [CVE-2026-0485] Denial of service (DOS) vulnerability in SAP BusinessObjects BI Platform BI-BIP-SRV | High | 7.5 |
| 3731908 | New | [CVE-2026-34256] Missing Authorization check in SAP ERP and SAP S/4 HANA (Private Cloud and On-Premise) CA-JVA-JVA | High | 7.1 |
| 3680767 | New | [CVE-2026-34264] Information Disclosure vulnerability in SAP Human Capital Management for SAP S/4HANA PA-PA-XX | Medium | 6.5 |
| 3715177 | New | [CVE-2026-27678] Missing Authorization check in SAP S/4HANA Backend OData Service (Manage Reference Structures) PM-EQM-RS | Medium | 6.5 |
| 3715097 | New | [CVE-2026-27677] Missing Authorization check in SAP S/4HANA OData Service (Manage Reference Equipment) PM-EQM-EQ | Medium | 6.5 |
| 3696239 | New | [CVE-2025-64775] Denial of Service Vulnerability in SAP BusinessObjects Business Intelligence Platform BI-BIP-SEC | Medium | 6.5 |
| 3705094 | New | [CVE-2026-34261] Missing Authorization check in SAP Business Analytics and SAP Content Management PA-OS | Medium | 6.5 |
| 3716767 | New | [CVE-2026-27679] Missing Authorization check in SAP S/4HANA Frontend OData Service (Manage Reference Structures) PM-EQM-RS | Medium | 6.5 |
| 3689080 | Update | [CVE-2026-24316] Server-Side Request Forgery (SSRF) in SAP NetWeaver Application Server for ABAP BC-TWB-TST-ECA | Medium | 6.4 |
| 3692004 | New | [CVE-2026-34257] Open Redirect vulnerability in SAP NetWeaver Application Server ABAP BC-FES-ITS | Medium | 6.1 |
| 3719397 | New | [CVE-2026-27674] Code Injection vulnerability in SAP NetWeaver Application Server Java (Web Dynpro Java) BC-WD-JAV | Medium | 6.1 |
| 3645228 | New | [CVE-2026-0512] Cross-Site Scripting (XSS) vulnerability in SAP Supplier Relationship Management (SICF Handler in SRM Catalog) SRM-EBP-CAT | Medium | 6.1 |
| 3730639 | New | [CVE-2026-34262] Information Disclosure Vulnerability in SAP HANA Cockpit and HANA Database Explorer HAN-CPT-CPT2-DBX | Medium | 5.0 |
| 3703813 | New | [CVE-2026-27673] Missing Authorization Check in SAP S/4HANA (Private Cloud and On-Premise) IS-U-TO-MI | Medium | 4.9 |
| 3703276 | New | [CVE-2026-27672] Missing Authorization check in Material Master Application SCM-BAS-INT-MD | Medium | 4.3 |
| 3711682 | New | [CVE-2026-27676] Missing Authorization check in SAP S/4HANA OData Service (Manage Technical Object Structures) PM-EQM-RS | Medium | 4.3 |
| 3530544 | Update | [CVE-2025-42899] Missing Authorization check in SAP S4CORE (Manage Journal Entries) FI-FIO-GL-TRA | Medium | 4.3 |
| 3702191 | New | [CVE-2026-24318] Insecure Session Management vulnerability in SAP BusinessObjects Business Intelligence Platform BI-BIP-INV | Medium | 4.2 |
| 3698216 | New | [CVE-2026-27683] Reflected cross site scripting vulnerability in SAP BusinessObjects Business Intelligence Platform BI-BIP-INV | Medium | 4.1 |
| 3665042 | Update | [CVE-2026-27680] CSS Injection vulnerability in SAP NetWeaver Application Server ABAP BC-WD-UR | Low | 3.1 |
| 3723097 | New | [CVE-2026-27675] Code Injection vulnerability in SAP Landscape Transformation CA-LT-PCL | Low | 2.0 |
As always, the Onapsis Research Labs is already updating The Onapsis Platform to incorporate the newly published vulnerabilities into the product so that our customers can protect their businesses.
For more information about the latest SAP security issues and our continuous efforts to share knowledge with the security community, subscribe to our monthly Defender’s Monthly Newsletter.
