SAP Security Notes: March 2026 Patch Day
HotNews Notes for SAP Quotation Management Insurance application and SAP NetWeaver Enterprise Portal Administration
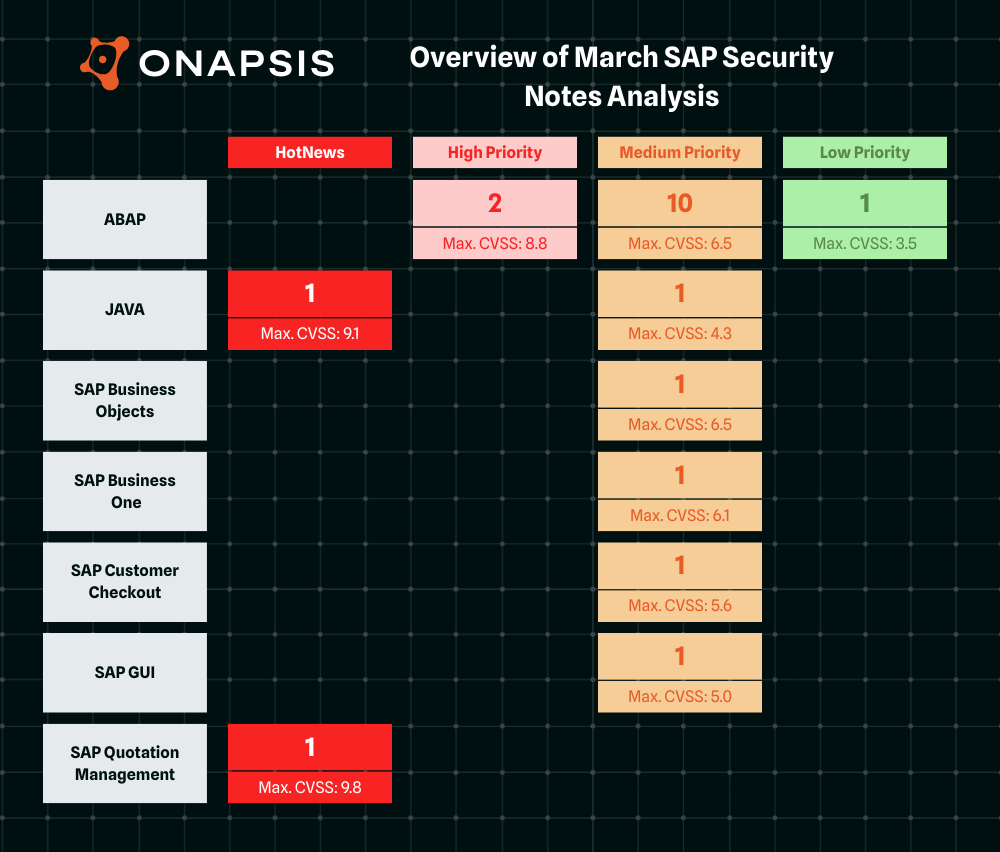
Highlights of March SAP Security Notes analysis include:
- March Summary – Twenty new and updated SAP security patches released, including two HotNews Notes and two High Priority Notes
- Log4j again… – Vulnerable Log4j artifact in SAP Quotation Management Insurance application allows execution of arbitrary code on the server
- Onapsis Research Labs Contribution – Our team supported SAP in patching the vulnerability CVE-2026-27689.
SAP has published twenty new and updated SAP Security Notes in its March Patch Day, including two HotNews Notes and two High Priority Notes. One of the sixteen new SAP Security Notes was published in collaboration with the Onapsis Research Labs. Additional credits were issued to our Onapsis Research Labs for a HotNews Note in January 2026 patching two vulnerabilities.
The HotNews Notes in Detail
SAP’s March Patch Day comes with two new HotNews Notes.
SAP Security Note #3698553, tagged with a CVSS score of 9.8, patches a Code Injection vulnerability in SAP Quotation Management Insurance application (FS-QUO). The application uses an outdated artifact of Apache Log4j 1.2.17 that is vulnerable to CVE-2019-17571. It allows an unprivileged attacker to execute arbitrary code remotely on the server, causing high impact on confidentiality, integrity, and availability of the application.
SAP Security Note #3714585 is tagged with a CVSS score of 9.1 and patches an Insecure Deserialization vulnerability in SAP NetWeaver Enterprise Portal Administration. Due to missing or insufficient validation during the deserialization of uploaded content, a privileged user is able to upload untrusted or malicious content. Only the fact that an attacker requires high privileges for a successful exploit prevents the vulnerability from being tagged with a CVSS score of 10.
The High Priority Notes in Detail
The Onapsis Research Labs (ORL) contributed to patching the only new High Priority Note of this patch day.
SAP Security Note #3719502, tagged with a CVSS score of 7.7, patches a Denial of Service vulnerability in SAP Supply Chain Management. The ORL team detected a remote-enabled function module which processes a loop where the number of iterations can be specified externally via an input parameter. An authenticated attacker with regular user privileges and network access could repeatedly invoke this function module, consuming excessive system resources and potentially rendering the system unavailable. SAP has patched the issue by introducing a hard-coded limit of 30.000 loop steps.
SAP Security Note #3697567 was initially released on SAP’s February Patch Day. The note is tagged with a CVSS score of 8.8 and patches an XML Signature Wrapping vulnerability in SAP NetWeaver AS ABAP and ABAP Platform. The note was updated with minor text changes in the ‘Solution’ section.
Onapsis Contribution
SAP patched the vulnerability CVE-2026-27689, a denial of service vulnerability with CVSS of 7.7, releasing the High Priority SAP Security Note #3719502.
Summary & Conclusions
With twenty SAP Security Notes, including two new HotNews and one new High Priority Note, SAP’s March Patch Day is once again a busy one. We are glad that our Onapsis Research Labs could support SAP in patching a High Priority vulnerability that could allow attackers to render customer systems completely unavailable.
| SAP Note | Type | Description | Priority | CVSS |
| 3698553 | New | [CVE-2019-17571 ] Code Injection vulnerability in SAP Quotation Management Insurance application (FS-QUO) FS-QUO | HotNews | 9.8 |
| 3714585 | New | [ CVE-2026-27685] Insecure Deserialization in SAP NetWeaver Enterprise Portal Administration BC-PIN-PCD | HotNews | 9.1 |
| 3697567 | Update | [CVE-2026-23687] XML Signature Wrapping in SAP NetWeaver AS ABAP and ABAP Platform BC-SEC-WSS | High | 8.8 |
| 3719502 | New | [CVE-2026-27689] Denial of service (DOS) in SAP Supply Chain Management SCM-APO-INT-EXT | High | 7.7 |
| 3695912 | Update | [CVE-2026-24324] Denial of service (DOS) vulnerability in SAP BusinessObjects Business Intelligence Platform (AdminTools) BI-BIP-SRV | Medium | 6.5 |
| 3672622 | Update | [CVE-2026-0484] Missing Authorization check in SAP NetWeaver Application Server ABAP and SAP S/4HANA BC-DWB-CEX-CF | Medium | 6.5 |
| 3697355 | New | [CVE-2026-27684] SQL Injection Vulnerability in SAP NetWeaver (Feedback Notification) CA-NO | Medium | 6.4 |
| 3689080 | New | [CVE-2026-24316] Server-Side Request Forgery (SSRF) in SAP NetWeaver Application Server for ABAP BC-TWB-TST-ECA | Medium | 6.4 |
| 3703856 | New | [CVE-2026-24309] Missing Authorization check in SAP NetWeaver Application Server for ABAP BC-DB-ORA-CCM | Medium | 6.4 |
| 3693543 | New | [CVE-2026-0489] DOM-based Cross-Site Scripting (XSS) Vulnerability in SAP Business One (Job Service) SBO-CRO-SEC | Medium | 6.1 |
| 3703385 | New | [CVE-2026-27686] Missing Authorization check in SAP Business Warehouse (Service API) BC-BW | Medium | 5.9 |
| 3701020 | New | [CVE-2026-27687] Missing Authorization check in SAP S/4HANA HCM Portugal and SAP ERP HCM Portugal PY-PT | Medium | 5.8 |
| 3708457 | New | [CVE-2026-24311] Insecure Storage Protection vulnerability in SAP Customer Checkout 2.0 IS-SE-CCO | Medium | 5.6 |
| 3707930 | New | [CVE-2026-24313] Missing Authorization check in SAP Solution Tools Plug-In (ST-PI) SV-SMG-SDD | Medium | 5 |
| 3704740 | New | [CVE-2026-27688] Missing Authorization check in SAP NetWeaver Application Server for ABAP BC-DB-SDB | Medium | 5 |
| 3699761 | New | [CVE-2026-24317] DLL Hijacking vulnerability in SAP GUI for Windows with active GuiXT BC-FES-GXT | Medium | 5 |
| 3396109 | Update | [CVE-2024-22128] Cross-Site Scripting (XSS) vulnerability in SAP NetWeaver Business Client for HTML BC-FES-BUS | Medium | 4.7 |
| 3700960 | New | [Multiple CVEs] Denial of Service due to Outdated OpenSSL Version in SAP NetWeaver AS Java (Adobe Document Services) BC-SRV-FP | Medium | 4.3 |
| 3646297 | New | [CVE-2026-24314] Information Disclosure vulnerability in SAP S/4HANA (Manage Payment Media) FI-FIO-AP-PAY | Medium | 4.3 |
| 3694383 | New | [CVE-2026-24310] Missing Authorization check in SAP NetWeaver Application Server for ABAP BC-DB-INF | Low | 3.5 |
As always, the Onapsis Research Labs is already updating The Onapsis Platform to incorporate the newly published vulnerabilities into the product so that our customers can protect their businesses.
For more information about the latest SAP security issues and our continuous efforts to share knowledge with the security community, subscribe to our monthly Defender’s Monthly Newsletter.
